 The notorious Necurs botnet is one of the oldest and largest spam and phishing delivery systems in existence. It controls millions of machines that the criminal botmasters use to send malicious payloads. Necurs has now adopted a retro trick to make itself more evasive and less likely to have its phishing intercepted by your filters.
The notorious Necurs botnet is one of the oldest and largest spam and phishing delivery systems in existence. It controls millions of machines that the criminal botmasters use to send malicious payloads. Necurs has now adopted a retro trick to make itself more evasive and less likely to have its phishing intercepted by your filters.It's begun emailing archive files that unzip to a file with a .url extension. This commonplace Windows shortcut opens a page directly in a browser. The advantage of this approach is that it's typically overlooked by email scanners, which are hunting for more complicated infection chains. The final destination of this link is a remote script file that downloads and automatically executes a malicious payload.
This common Windows shortcut is the social engineering tactic which tricks your users into thinking the email file attachment they just unzipped has created a folder that they need to enter and view the actual file.
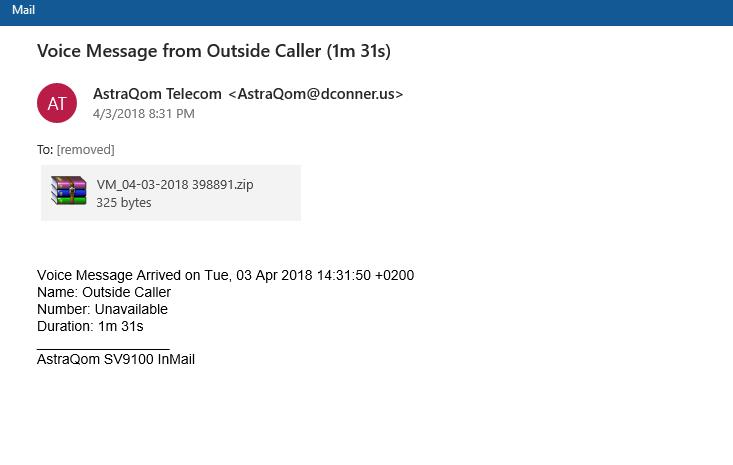
Unfortunately, this is what crooks want because trying to access this faux folder will launch the infection chain. This time, they are exploiting the power of simplicity. Here is how the Phish looks:
Your email filters usually apply preset rules, and this particular vector is probably not among them, so update your filter settings. Interestingly, Necurs does not infect computers using Russian as a language.
I suggest you send this email to your employees, friends and family. Feel free to copy/paste/edit:
There is a new email scam you need to watch out for. Bad guys are sending emails that have an archive file as an attachment. They often look like a voice mail message you have missed. Assume these attachments files are guilty until proven innocent!
Do not click on the zip file to listen to the message, delete the file or click on the Phish Alert Button to forward it to IT and delete if from your inbox.
It's clear you just have to train your users ASAP.
I strongly suggest you get a quote for new-school security awareness training for your organization and find out how affordable this is. You simply have got to start training and phishing your users ASAP because your filters have an average 10.5% failure rate. Get a quote now and you will be pleasantly surprised.
Don't like to click on redirected buttons? Cut & Paste this link in your browser:
https://info.knowbe4.com/kmsat_get_a_quote_now
Let's stay safe out there.
Warm regards,
Stu Sjouwerman,
Founder and CEO, KnowBe4, Inc

Technical background at Trent Micro: https://blog.trendmicro.com/trendlabs-security-intelligence/necurs-evolves-to-evade-spam-detection-via-internet-shortcut-file/





