Reporters investigating Russian military intelligence have been targeted by highly sophisticated cyber attacks through their encrypted email accounts, with evidence suggesting Moscow was responsible, the email service provider ProtonMail and journalists said on Saturday.
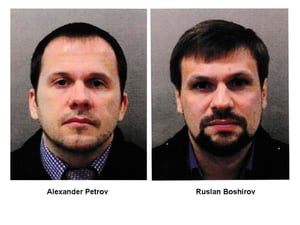
The phishing attack, which sought to dupe users into sharing their ProtonMail passwords, was aimed at journalists from the award-winning website Bellingcat, which helped identify the agents who poisoned former Russian spy Sergei Skripal in Britain.
Bellingcat, a highly regarded Britain-based investigative website, has used open-source technology to break a series of stories, notably concerning Russia, including major revelations in the downing of MH17 flight over eastern Ukraine, which has also been linked to Russia's GRU intelligence service.
Geneva-based ProtonMail said in a statement that "the evidence (along with independent third-party assessments) seem to suggest an attack of Russian origin." The company's chief executive Andy Yen told the AFP news agency that the operation "was one of the best-run phishing attacks we have ever seen."
Bellingcat journalist Christo Grozev, who led the site's work on the Skripal case, said he had no doubt Russia's GRU military intelligence unit was responsible and that it marked "a quantum leap" in terms of their technical sophistication.
"It was very convincing," he told AFP, noting that no Bellingcat reporters gave up their passwords. Source and Story continued at TheLocal.ch
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before the bad guys do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
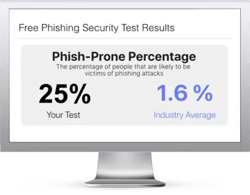 Here's how it works:
Here's how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don't like to click on redirected buttons? Cut & Paste this link in your browser:
https://www.knowbe4.com/phishing-security-test-offer





