Threatpost reported that the notorious Necurs botnet is back in business, after mysteriously going dark for nearly a month. Researchers report the Necurs has returned to spewing massive volumes of email containing an improved version of the potent Locky ransomware and the Dridex banking Trojan.
According to reports which have been tracking Necurs, criminals behind the botnet began pushing out multimillion email message campaigns on Monday. This new activity is the first life seen from the Necurs Botnet since it went dark on May 31.
Necurs is widely believed to be one of the largest botnets (with 6.1 million bots) functioning and responsible for millions in dollar losses tied to ransomware and Dridex banking Trojan infections.
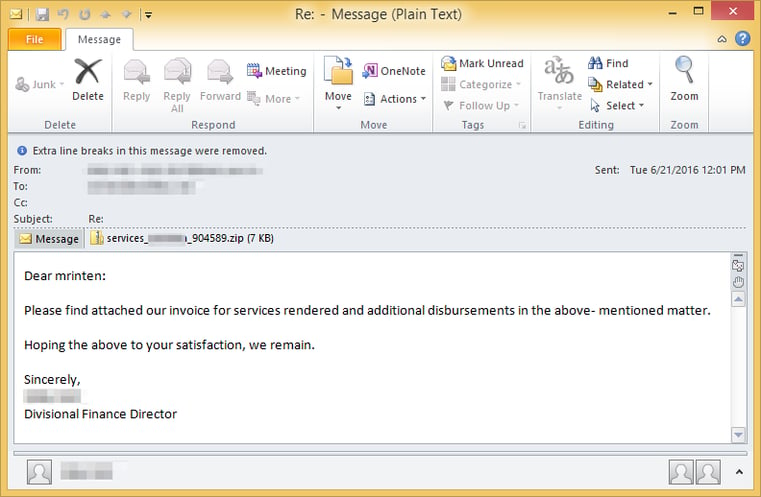
Here is how the email messages look: "Dear (random name): Please find attached our invoice for services rendered and additional disbursements in the above-mentioned matter. Hoping the above to your satisfaction, we remain. Sincerely, (random name and title). "
The Locky campaigns included zip attachments containing JavaScript code, and the new loader component to Locky included new anti-analysis tricks. One of those tricks includes detecting whether or not it is running within a sandbox test environment versus a live infection. It does this via a complicated mathematical analysis measuring the time it take for the ransomware to execute API calls. “The malware compares the number of CPU cycles that it takes to execute certain Windows APIs. As you would expect, it takes more cycles in a VM environment to execute most Windows functions.”
A second obfuscation technique includes what Epstein called a “tap dance within memory” for the cross-module execution of the Locky payload. Through a complex series of steps that include unpacking the Locky binary via RtlDecompressBuffer and overwriting the original loader image, attackers can relocate Locky instruction code in order to make manual analysis of memory dumps more difficult. Epstein says they are already tracking an escalation of Locky campaigns since Necurs came back online. He estimates Necurs is pushing out 80 to 100 million email messages each day.




