 The malwareless and seemingly benign nature of business email compromise emails, mixed with impersonation techniques, are difficult to spot as being malicious, making them even more dangerous.
The malwareless and seemingly benign nature of business email compromise emails, mixed with impersonation techniques, are difficult to spot as being malicious, making them even more dangerous.
I’ve covered both the threat of business email compromise and response-based email attacks before. How can I not? They are prominent techniques used by phishing scammers everywhere. But it’s the reported combination of the two by Phish Labs that has me concerned. Representing the overwhelming lion’s share of all email threat volume reported, the use of such business-toned, long-tailed email attacks are a greater danger to organizations
Take the following example, provided by Phish Labs:
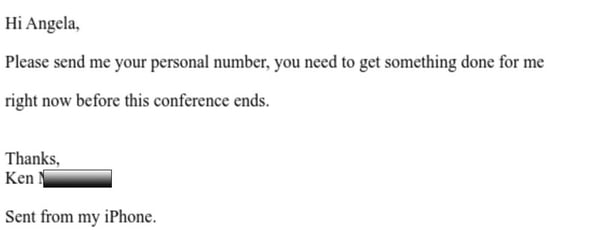
Source: Phish Labs
Note there’s no malicious attachment or link that a security solution can scan. This is pure social engineering; the assumption is that Angela either works directly for Ken or Ken is a few rungs higher in the corporate ladder. So, the urgency is created not in the message’s tone, but in the establishing of who is sending the email and what’s being asked. Additionally, the request for a mobile phone is to take the conversation to a medium where there is no sender email to verify, and so that the conversation is controlled.
These kinds of emails are why users within organizations need to undergo continual Security Awareness Training so that they maintain a sense of vigilance – especially when an email comes in that feels like there’s zero maliciousness to it.
 CEO fraud has ruined the careers of many executives and loyal employees, causing over $26 billion in losses. Don’t be the next victim. This manual provides a thorough overview of how executives are compromised, how to prevent such an attack and what to do if you become a victim.
CEO fraud has ruined the careers of many executives and loyal employees, causing over $26 billion in losses. Don’t be the next victim. This manual provides a thorough overview of how executives are compromised, how to prevent such an attack and what to do if you become a victim.




