Attacks leveraging look-alike federated logon pages are more dangerous than malware-laden attachments in email.
As you build out your security strategy to prevent successful cyber attacks, much of it focuses on stopping malware attempting to enter via email-based phishing attacks. It’s a priority, as 93% of data breaches start with phishing. But, cyber criminals are changing tactics, looking for ways to slip past your security measures and move their evil plans forward.
One such method if the use of phishing sites with federated replica sign-ins giving users multiple ways to “authenticate”. These sites are meticulously crafted to look like their legitimate counterparts, using just about any means of getting your user’s attention - pop-ups, ads, search results, social media, chat and IM applications, rogue browser extensions, web freeware, and “trusted” apps downloaded from app stores. As part of the scam, the process of authenticating is made to seem expected to the user. The goal is to trick them into giving up their credentials for use as part of a larger attack.
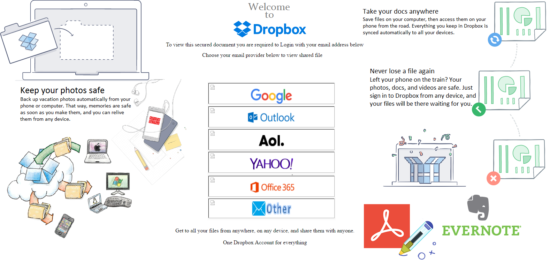
This scam plays on the mind, giving priority to expected and well-known visual cues – in this case familiar logon dialog boxes, branding, logos, and placement. The more accurate the copy, the more likely the user will become a victim.
The dangerous part of this kind of phishing attack is that there is no malicious code to detect, with the sites only staying up for a number of hours to avoid being blacklisted by security solutions. Because of the nature of the attack, these attacks are easily able to bypass security measures.
With 22% of employees clicking on at least one phishing email in the last year, and the abundance of user interaction with the web in its various forms, all mixed with the use of replicated sign-ins to steal credentials, organizations need to take this threat seriously.
Because this threat isn’t normally caught by traditional security solutions, organizations need to arm users with Security Awareness Training, educating them on tactics used, and how to spot a scam or attack before they become a victim.




