In today's connected world, nearly everyone has a story where they have been targeted by a scam and either that person or someone they know have lost money to scams.
In today's connected world, nearly everyone has a story where they have been targeted by a scam and either that person or someone they know have lost money to scams.
Just recently in the run up to Easter, people were receiving WhatsApp messages stating that Cadbury’s were giving away Easter eggs. All they had to do was click on the link to claim free chocolate Easter eggs. The link however, took people to a page which asked for personal information and never actually intended to send off any chocolate treats. The scam spread so fast that Cadbury’s had to issue a formal statement that they had nothing to do with the elaborate game of “find the Easter egg” and that it was a scam.
But how can one identify scams, and perhaps more importantly, help friends and family who may not be so tech savvy to identify and avoid falling victim to scams?
Perhaps the most important thing to understand is that scammers will try to pull on an emotional string in order to get a reaction from someone. If anyone ever receives an email, an instant message, an SMS or even a phone call that invokes an emotional response and asks them to take immediate action, they should consider this to be a big red flag and not proceed.
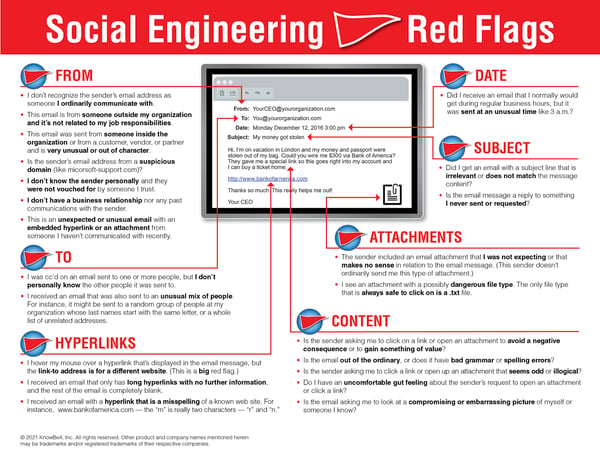
Our infographic "22 Social Engineering Red Flags" is a great resource and a reminder of what to watch out for in potential phishing emails:
Cybercriminal tactics can vary, but broadly speaking, these scams will often fall into the buckets of money, employment, love or threats.
Money appeals to everyone's greed. Whether that be actual money, or, in the above example, the promise of chocolate eggs. Who doesn’t like something for free? These types of scams usually fall into the category of “if it is too good to be true, it usually is.”
Employment scams are a variation of money scams in that they try to entice people with promises of lucrative jobs or work from home opportunities. Many times, these will ask for a lot of personal information and even payment up front as a service fee. Other times, criminals will use this tactic to recruit unwitting victims into inadvertently laundering money for them, leaving them not just financially worse off, but with potential legal consequences.
Love or dating scams are where criminals create fake profiles on dating sites and spend a long amount of time building up trust with their victims. Victims in these cases are often lonely individuals, even elderly. Once trust is established, the victims will begin to ask for favours or payment. These often begin small, but often escalate very quickly. A close family member may need expensive medical treatment or they may need money to visit the victim, which does not actually happen.
Threat-based scams often take the form of masquerading as a popular provider. For example, people may receive an email from Apple or Netflix stating that they have made a large purchase or that their service is about to be disconnected unless immediate action is taken. People out of fear of facing a large bill or losing service will not check the legitimacy of these emails and will act impulsively, playing into the criminal’s hands.
The important thing to remember for everyone is that there is never a need to act immediately on any notification. There is always time to double check the request by contacting the service provider directly, or asking the advice of someone else. Blindly following instructions or forwarding on unbelievable offers only helps criminals win.