 The Police Department in Cockrell Hill, Texas released in a press release that they lost 8 years worth of evidence after the department's server was infected with ransomware.
The Police Department in Cockrell Hill, Texas released in a press release that they lost 8 years worth of evidence after the department's server was infected with ransomware.
The lost evidence includes all body camera video, and sections of in-car video, in-house surveillance video, photographs, and all their Microsoft Office documents. OUCH.
Eight years worth of evidence lost
Some of the lost data goes back to 2009, there are some files that era that are backed up on DVDs and CDs and remained available.
"It is [...] unknown how many videos or photographs that could have assisted newer cases will not be available, although the number of affected prosecutions should remain relatively small," the press release reads.
In an interview with WFAA, who broke the story, Stephen Barlag, Cockrell Hill's police chief, said that none of the lost data was critical. The department also notified the Dallas County District Attorney's office of the incident.
Backup Procedure Kicked In After Locky Infection
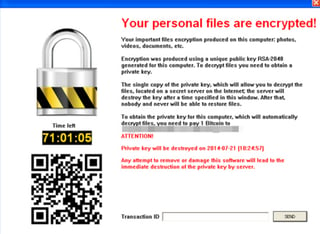
The department says the infection was discovered on December 12, last year, and the crooks asked for a $4,000 ransom fee to unlock the files.
After consulting with the FBI's cyber-crime unit, the department decided to wipe their data server and reinstall everything. Data could not be recovered from backups, as the backup procedure kicked in shortly after the ransomware took root, and backed up copies of the encrypted files. OUCH.
Infection Source: Phishing email with spoofed address
The press release says the infection took place after an officer opened a spam message from a cloned (spoofed) email address imitating a department issued email address. New-school security awareness training would highly likely have prevented this.
The infection did not spread to other computers because the server was taken offline and disconnected from the local network as soon as staff discovered the ransom demand. The department also said there was no evidence of data exfiltration to a remote server.
Hat Tip to Bleepingcomputer.
Can Your Domain Be Spoofed?
Are you aware that one of the first things hackers try is to see if they can spoof the email address of your CEO? If they are able to commit "CEO Fraud", penetrating your network is like taking candy from a baby.
Would you like to know if hackers can spoof your domain? KnowBe4 can help you find out if this is the case with our free Domain Spoof Test. It's quick, easy, and often a shocking discovery.
Find out now if your email server is configured correctly, our tests over the last 2 years show that 82% of servers fail to handle spoofed emails correctly.
PS, don't like to click on redirected buttons? Cut & paste this link in your browser:




