
Midsize and enterprise organizations take notice: the average and median amount of a ransom payment and the median size of the victim organization are on the rise.
If you’re at all concerned about ransomware (and you should be), the latest details from ransomware response vendor Coveware’s latest Quarterly Ransomware Report should have your attention.
According to the report, the median company size of victim organizations shot up 42% from last quarter to 391. At the same time, the trending for both average and median ransom payment sizes are also increasing (despite a dip this quarter). One of the concerns raised by Coveware is the motivation behind this “big game hunting” by ransomware gangs and affiliates is a “lack of economic alternatives” (read: other ways to make money).
Also of concern is the primary initial attack vector, which continues to be phishing (despite a slight dip this quarter), with RDP trending downward (as organizations continue to kill externally-facing remote access), and vulnerabilities are trending somewhat flat.
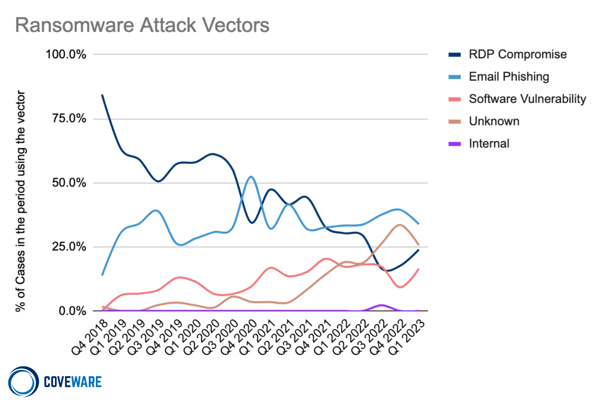
Source: Coveware
This continual dominance of phishing shows the leverage it provides attackers with an ability to gain access, persistence, control, stealth, and eventually enough privilege and lateral movement to successfully infect the organization with ransomware. Phishing can be stopped by a combination of solutions that include email scanning, endpoint protection, and Security Awareness Training.
 Here's how it works:
Here's how it works:




