 There has been a whopping 3500% increase in ransomware domains in the first quarter of 2016, compared to the last quarter of 2015. Those are the highlights of a new report by network control company Infoblox.
There has been a whopping 3500% increase in ransomware domains in the first quarter of 2016, compared to the last quarter of 2015. Those are the highlights of a new report by network control company Infoblox.
The Infoblox DNS Threat Index is an indicator of malicious infrastructure-building activity worldwide that exploits the Domain Name System (DNS). Cybercriminals create new domains as a foundation for unleashing a variety of threats ranging from malware to exploit kits, phishing, distributed denial of service (DDoS) attacks, and data exfiltration.
This index is a good indicator for future attacks
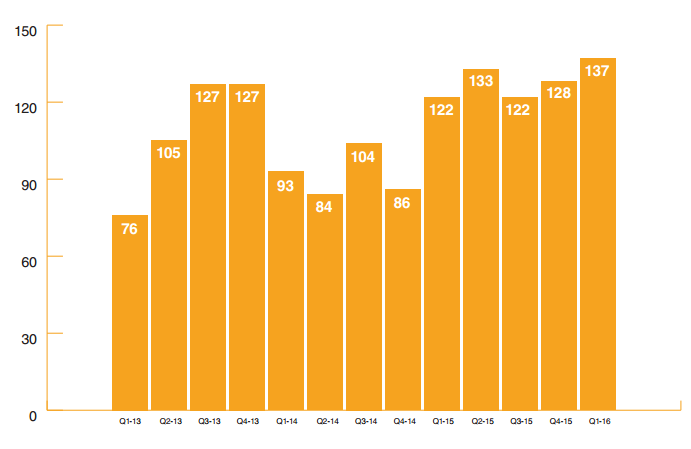
According to the latest Threat Index, this huge spike has pushed the overall threat index to its highest level ever recorded. It currently sits at level 137, up seven percent from level 128 in Q4 2015. The highest ever level recorded before this one was 133, back in Q2 2015.
The US hosts the biggest number of these domains, 41% which is usual, while the bad guys have decide to ditch Germany which dropped from 20% down to 2%.
“Cybercriminals are as likely as anyone else to take advantage of sophisticated infrastructure, and all of the countries in this quarter’s list fit that description,” said Lars Harvey, vice president of security strategy at Infoblox. “But the geographic spread shows that much like cockroaches that scurry from the light, cybercriminals are quick to shift to a more advantageous location as needed.”
Shift from small-dollar heists targeting consumers to larger, more profitable attacks on commercial entities
They observed: "What has changed over the past quarter or two is a shift from small-dollar heists targeting consumers to larger, more profitable attacks on commercial entities. And as news of this success has spread, certainly through underground networks and ironically through general media coverage of the danger, cybercriminals have apparently taken notice.
Ransomware now 60 percent of the entire malware category
"In Q1 2016 this led to a 35-fold increase in observations of ransomware-related domains (both those hosting the malicious downloads and those that malware communicates with once installed), propelling it to account for 60 percent of the entire malware category. By far the most observed instance of ransomware was “Locky” – the same variant that Forbes Magazine identified as the culprit in the Los Angeles hospital attack. According to the FBI, ransomware victims reported costs of $209 million in the first quarter, compared to $24 million for all of 2015. It is unclear how much of this may have taken the form of direct payments to cybercriminals, which in turn would fund more crime."
 This 26-page manual is packed with actionable info that you need to prevent infections, and what to do when you are hit with ransomware. You also get a Ransomware Attack Response Checklist and Prevention Checklist. You will learn more about:
This 26-page manual is packed with actionable info that you need to prevent infections, and what to do when you are hit with ransomware. You also get a Ransomware Attack Response Checklist and Prevention Checklist. You will learn more about:




