 KnowBe4 reports on the top-clicked phishing emails by subject lines each quarter in three different categories: subjects related to social media, general subjects, and 'In the Wild' - we get those results from the millions of users that click on our Phish Alert Button to report real phishing emails and allow our team to analyze the results.
KnowBe4 reports on the top-clicked phishing emails by subject lines each quarter in three different categories: subjects related to social media, general subjects, and 'In the Wild' - we get those results from the millions of users that click on our Phish Alert Button to report real phishing emails and allow our team to analyze the results.
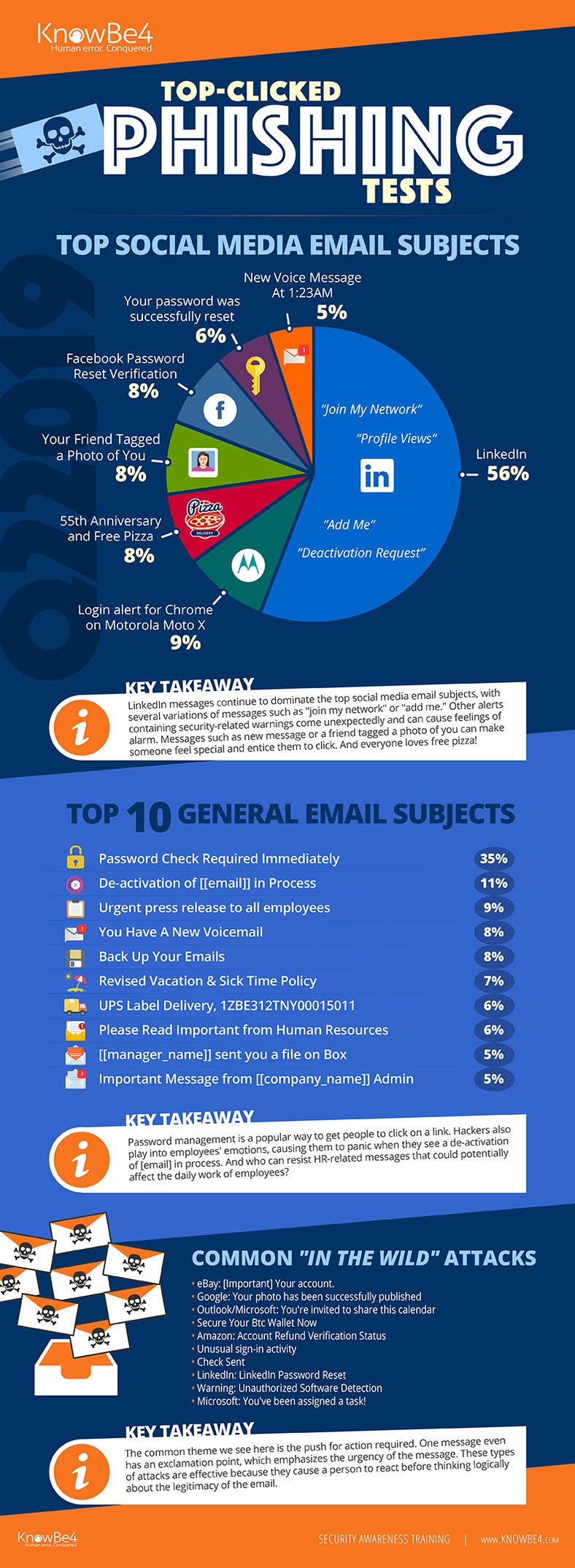
LinkedIn Continues To Fool Users
Last quarter, more than half of all social media-related phishing emails imitated LinkedIn messages. This trend has been increasing quarter over quarter, likely because there is a perception that they would be legitimate coming from a professional network. It's a significant problem because many LinkedIn users have their accounts tied to their corporate email addresses.
Such a high percentage increases corporate risk of a phishing attack, ransomware breach or other social engineering-related threat. Social media sites in general are being used by cybercriminals as phish bait more and more each quarter. According to recent research from Vade Secure, social media phishing attacks are up by more than 70%.
“It feels good to ‘join my network’ or connect with someone in some way – that’s why social media phishing attacks are so successful,” said Stu Sjouwerman, CEO of KnowBe4. “Users innately trust their ‘verified’ contacts so are more apt to click on a link that come from someone they know. It’s becoming harder to identify phishing attacks, but our users are smarter than the bad guys think and can absolutely be trained to identify and avoid phishing and social engineering attacks."
Password Management and Actions Required Are Popular Ploys
Aside from social media-related messages, general subject lines related to password management were highest on the list. In-the-wild attacks – those that were actual phishing emails and not KnowBe4 testing emails – found greatest success when they asked for action from the recipient, such as being invited to share an Outlook calendar or being assigned a task in a Microsoft platform. This comes as no surprise as 80% of all brand deception phishing scams targeting execs pretend to be from Microsoft.
See the Infographic with All Top Messages in Each Category for Last Quarter:
Click here to download the full infographic (PDF) Great to share with your users!
Top-Clicked Social Media Related Subjects in Q2 2019:
- LinkedIn: Profile Views, Join my network, Add me to your network, Deactivation Request
- Login alert for Chrome on Motorola Moto X
- 55th Anniversary and Free Pizza
- Your Friend Tagged a Photo of You
- Facebook Password Reset Verification
- Your password was successfully reset
- New voice message at 1:23AM
Top 10 Most-Clicked General Email Subjects in Q2 2019:
- Password Check Required Immediately
- De-activation of [[email]] in Process
- Urgent press release to all employees
- You Have A New Voicemail
- Back Up Your Emails
- Revised Vacation & Sick Time Policy
- UPS Label Delivery, 1ZBE312TNY00015011
- Please Read Important from Human Resources
- [[manager_name]] sent you a file on Box
- Important Message from [[company_name]] Admin
Most Common 'In the Wild' Attacks in this period were:
- eBay: [Important] Your account.
- Google: Your photo has been successfully published
- Outlook/Microsoft: You're invited to share this calendar
- Secure Your Btc Wallet Now
- Amazon: Account Refund Verification Status
- Unusual sign-in activity
- Check Sent
- LinkedIn: LinkedIn Password Reset
- Warning: Unauthorized Software Detection
- Microsoft: You've been assigned a task!
*Capitalization and spelling are as they were in the phishing test subject line.
**Email subject lines are a combination of both simulated phishing templates created by KnowBe4 for clients, and custom tests designed by KnowBe4 customers.
See results from all previous quarters here: https://blog.knowbe4.com/topic/top-clicked-phishing-email-subjects
Free Social Media Phishing Test
Would your users fall for a phishing email that looks like it originated from a credible social media site such as Facebook, LinkedIn or Twitter? Attackers use social media to target both your brand, your users, and even your customers by distributing malware or using social engineering to phish for credentials. These platforms have become a goldmine for the bad guys to carry out social media phishing attacks against your organization. Don't get hacked by social media phishing attacks!
 Here’s How the Social Media Phishing Test works:
Here’s How the Social Media Phishing Test works:
- Immediately start your test with your choice of three social media phishing templates
- Choose the corresponding landing page your users see after they click
- Show users which red flags they missed or send them to a fake login page
- Get a PDF emailed to you in 24 hours with your percentage of clicks and data entered
Don't like to click on redirected buttons? Copy & paste this link into your browser:
https://www.knowbe4.com/social-media-phishing-test





