 Every quarter, KnowBe4 reports on the top-clicked phishing emails by subject lines in three categories: Social, General, and 'In the Wild'. The latter category results come from the millions of users that click on our Phish Alert Button to report real phishing emails and allow our team to analyze the results.
Every quarter, KnowBe4 reports on the top-clicked phishing emails by subject lines in three categories: Social, General, and 'In the Wild'. The latter category results come from the millions of users that click on our Phish Alert Button to report real phishing emails and allow our team to analyze the results.
Social Media Is Now A Part Of Everyday Business
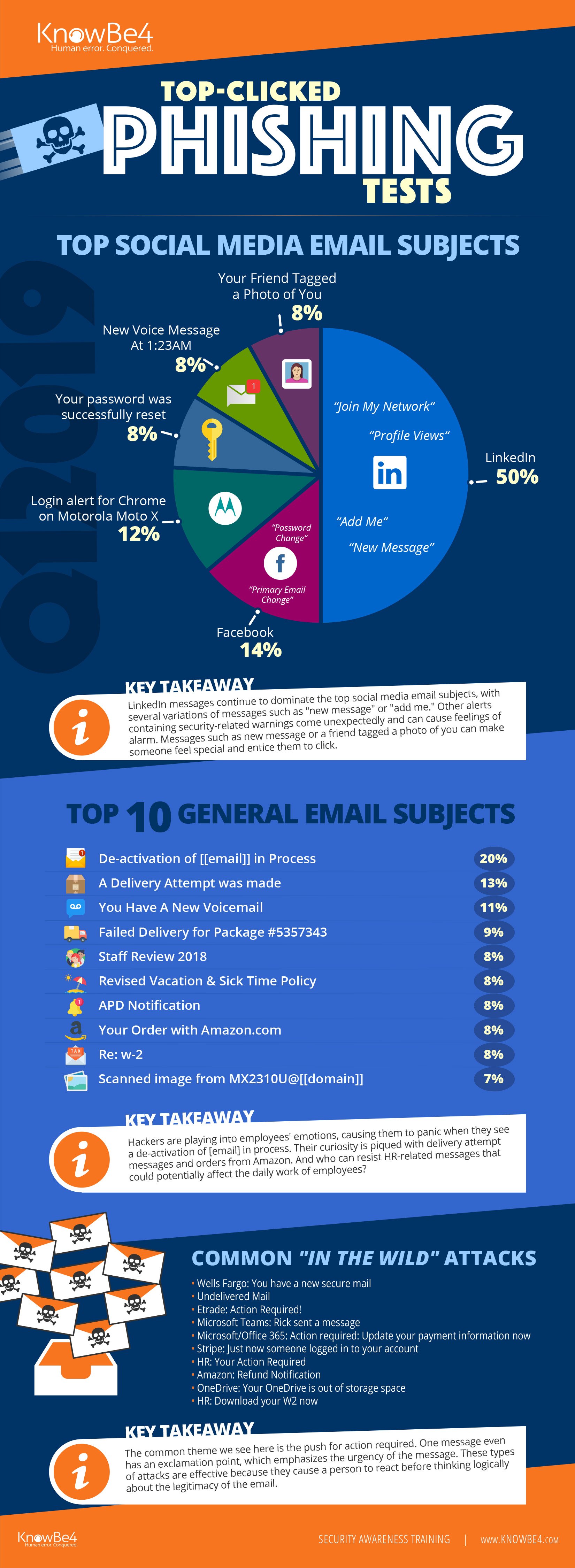
A major trend this quarter is that half of all social media-related subjects looked like they were coming from LinkedIn. We've seen this particular message type trending upward quarter over quarter, which is significant because many LinkedIn users have their accounts tied to their corporate email addresses.
Such a high percentage increases corporate risk of a phishing attack, ransomware breach or other social engineering-related threat. Social media sites in general are a crucial piece in the cybercrime economy. According to recent research from Bromium, cybercriminals earn at least $3.25B per year from social media-enabled cybercrime.
As tempting as it may be to click in emails to see who viewed your profile or who wants to connect, it's more important than ever to think before you click and log in to your account directly.
Hacker's Tap Into Emotions, Causing Panicked Reactions
Aside from social media-related messages, a lot of subject lines contained phrases like de-activation of email, failed delivery and action required to elicit a sense of urgency from the user. These types of attacks are effective because they cause a person to react without thinking logically about the legitimacy of the email. Notices about delivery attempts, Amazon orders, and HR-related messages also prove to bee too enticing to ignore for many users.
See the Infographic with All Top Messages in Each Category for Last Quarter:
Click here to download the full infographic (PDF) Great to share with your users!
Top-Clicked Social Media Related Subjects in Q1 2019:
- LinkedIn: Join my network, Profile Views, Add me to your network, New InMail Message
- Facebook: Password Change, Primary email changed
- Login alert for Chrome on Motorola Moto X
- Your password was successfully reset
- New voice message at 1:23AM
- Your Friend Tagged a Photo of You
Top 10 Most-Clicked General Email Subjects in Q1 2019:
- De-activation of [[email]] in Process
- A Delivery Attempt was made
- You Have A New Voicemail
- Failed Delivery for Package #5357343
- Staff Review 2018
- Revised Vacation & Sick Time Policy
- APD Notification
- Your Order with Amazon.com
- Re: w-2
- Scanned image from MX2310U@[[domain]]
Most Common 'In the Wild' Attacks in this period were:
- Wells Fargo: You have a new secure mail
- Undelivered Mail
- Etrade: Action Required!
- Microsoft Teams: Rick sent a message
- Microsoft/Office 365: Action required: Update your payment information now
- Stripe: Just now someone logged in to your account
- HR: Your Action Required
- Amazon: Refund Notification
- OneDrive: Your OneDrive is out of storage space
- HR: Download your W2 now
*Capitalization and spelling are as they were in the phishing test subject line.
**Email subject lines are a combination of both simulated phishing templates created by KnowBe4 for clients, and custom tests designed by KnowBe4 customers.
See results from all previous quarters here: https://blog.knowbe4.com/topic/top-clicked-phishing-email-subjects
Free Phish Alert Button
Do your users know what to do when new phishing attacks hit their inbox? KnowBe4's Phish Alert Button gives them a safe way to forward email threats to the security team for analysis and deletes the email from the user's inbox to prevent future exposure. All with just one click!
 Phish Alert benefits:
Phish Alert benefits:
- Reinforces your organization’s security culture
- Users can report suspicious emails with just one click
- Incident Response gets early phishing alerts from users, creating a network of “sensors”
- Email is deleted from the user's inbox to prevent future exposure
- Easy deployment via MSI file for Outlook, G Suite deployment for Gmail (Chrome)
Don't like to click on redirected links? Cut & Paste this link in your browser:





