By Eric Howes, KnowBe4 Principal Lab Researcher.
Over the past few months we've discussed the rising use of price discrimination among purveyors of ransomware to maximize their returns on ransomware campaigns. Instead of using poorly targeted "spray-and-pray" campaigns that extract a uniform toll (one or two bitcoins) from a random and diverse collection of victims, the bad guys are increasingly using more targeted campaigns that match the ransom demands with the victims' ability and willingness to pay.
One way the bad guys have incorporated price discrimination into their standard game is the use of backdoor trojans, sophisticated keyloggers, and full-blown RATs to reconnoiter potential marks and gather data about their business operations and finances. If they determine your organization is flush with cash or is uniquely sensitive to downtime or other disruptions in service, you can expect to pay more. Much, much more.
While this strategy may be useful and appropriate for larger, more lucrative targets, it doesn't scale well and, thus, wouldn't necessarily be appropriate for use with mass phishing campaigns designed to hit potential victims en masse with ransomware attacks.
In a recent blog post on BleepingComputer, however, our good friend Larry Abrams documents a new ransomware variant dubbed Fantom, which employs a simple, yet effective technique to wed basic price discrimination with mass, phishing-driven ransomware campaigns.
Enter the Fantom
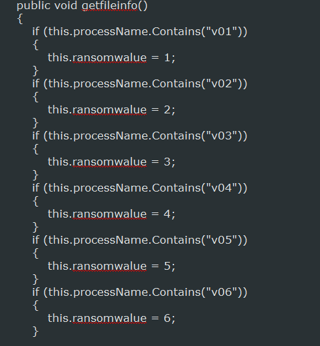
Fantom, which was discovered by the Malware Hunter Team, is a new ransomware variant that sports a number of interesting features, the most significant of which is the use of file and process names to set the size of the ransom demand. Put another way, after Fantom lands on a system it derives the ransom price to be demanded in the ransom note from its own file and process name, which is set by the malicious actor running the campaign. (Those interested in the peculiar mechanics through which Fantom does this should see Larry's article.)
It's a simple, straightforward technique that, when coupled with some diligent scouting and research of potential targets, allows ransomware purvyors to practice simple price discrimination on a mass scale. As Larry explains...
With this new variant of Fantom, the ransom amount is now determined by the name of the process. This allows the developer to create various distribution campaigns using the same exact sample, but request different ransom amounts depending on how the distributed file is named. For example, if the developer wanted to target home users, they may make the ransom amount lower than if they were targeting a particular business or organization simply by changing the filename.
For example, the bad guys might decide to go after hospitals and other health care providers as part of a semi-targeted ransomware campaign. These kinds of organizations are prime targets for hefty ransomware demands, since the nature of their business means they are particularly vulnerable or sensitive to downtime and service interruptions. It's also known at this point that such organizations are soft targets -- less well-defended than comparably sized organizations in other industries.
Having assembled a list of targets and harvested a list of email addresses associated with employees working for those targeted organizations, the malicious actors need only adjust the file name of the main ransomware executable to ratchet up the demanded ransom amount -- no code changes required.
The same bad guys could then turn around and run another campaign against differently selected category or group of targets by simply changing the file name to demand a lower ransom amount.
Fear the Fantom
Fantom has a number of other noteworthy features -- some unique, some not so unique but still relatively rare to find among the growing number of ransomware strains that have been seen in the wild over the past two or three years.
- operation independent of C&C server
- offline encryption (key generated based on random personal ID)
- offline decryption
- customized ransoms determined by file/process name
- customized payment email addresses determined by file/process name
- network share enumeration/decryption
- randomly generated wallpapers (for display of ransom demand)
What this interesting collection of features tells us is that the bad guys continue to experiment with new features and processes designed to make their ransomware operations more resilient and difficult to take down even as they adopt more sophisticated pricing techniques. Again, for more detail on these other features, see Larry's article at BleepingComputer.
Spawn of the Fantom
While it's always dangerous to speculate on the future development of malware (beyond to opine generally that it's a sure thing that the bad guys will continue to innovate around the ransomware model), Fantom's use of file and process names to facilitate basic price discrimination in mass-distributed ransomware campaigns looks to us like the kind of "feature" that could catch on among developers of competing ransomware families, particularly those who are in the RaaS (ransomware as a service) business.
If your company or organization has been skating along over the past year or so by paying the occasional nuisance ransom of 1-2 bitcoins after your employees get social engineered into opening phishing attachments and links, you may very well find this (non)strategy an increasingly costly one over the coming months. Ransomware purveyors are getting savvier about who can pay and how much, and that means the price to get your data back is going up -- way up.
With the bad guys getting savvier and more sophisticated, your own employees need to start stepping up their own security game. They are your company's last line of defense in the never-ending war being waged within inboxes across your organization. But those employees need good security awareness training to hone their security skills and become the security warriors you need them to be.
Download Your Ransomware Hostage Rescue Manual
Get the most complete (updated spring 2016) Ransomware Manual packed with actionable info that you need to have to prevent infections, and what to do when you are hit with ransomware.
If you do not like to click on buttons with redirects, cut/paste this link in your browser:
https://info.knowbe4.com/ransomware-hostage-rescue-manual-0





