 Motherboard reports that SIM swappers are launching phishing attacks against employees at Verizon, T-Mobile, and Sprint in order to hijack customer service tools. Once they have access to these tools, the hackers can take over phone numbers directly without having to trick an employee into performing each swap for them. The attackers are using phishing pages that spoof the login portals of VPNs that the companies use to access these tools.
Motherboard reports that SIM swappers are launching phishing attacks against employees at Verizon, T-Mobile, and Sprint in order to hijack customer service tools. Once they have access to these tools, the hackers can take over phone numbers directly without having to trick an employee into performing each swap for them. The attackers are using phishing pages that spoof the login portals of VPNs that the companies use to access these tools.
For example, Verizon uses a tool called “Omni,” which allows employees of Verizon and its authorized resellers to manage customer accounts. A former employee of a Verizon reseller told Motherboard that this tool could “definitely” be used to carry out SIM swapping attacks.
“Omni is a site that employees use to process things that customers come in store for that’s account related,” the former employee said. “So device and SIM changes, billing, usage related things, plans, and activations are processed through there....Once you’ve logged into an account, you can edit the ICCID [a SIM card's unique identification code] for a line being used. From there you pop the SIM card you swapped into a phone and then it’ll have the victim’s number, which will then be used for identity theft.”
In the past, SIM swaps generally involved an attacker calling up a telecom company under the guise of the victim. The attacker would then use social engineering to convince a telecom employee to transfer the victim’s phone number over to an attacker-controlled device. The attacker could then use the phone number to break into the victim’s online accounts and bypass SMS-based two-factor authentication.
The new technique described by Motherboard is much more efficient from an attacker’s point of view, since it allows them to remove the unwitting middleman and gain the same access as an employee.
Verizon, T-Mobile, and Sprint each told Motherboard that they’ve implemented mitigations against these attacks, but these measures aren’t foolproof. The former Verizon reseller employee said they received security training, but it didn’t include any information on this form of attack.
“We had a mandatory online training where we were instructed to be careful about phishing, but nothing else,” the former employee said. “I actually had to warn everyone in our company about the whole SIM swap scam going on and to be safe about it.”
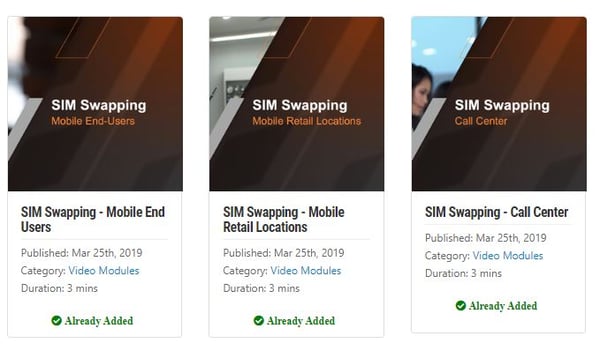
New-school security awareness training can ensure your employees receive up-to-date knowledge on the current threat landscape facing your industry. KnowBe4 has 3 training modules by Kevin Mitnick specifically created for this type of fraud for Mobile end-users, Retail Locations, and Call Centers. You can scroll down and create a free account in KnowBe4's ModStore and see these for yourself.
Motherboard has the story: https://www.vice.com/en_us/article/v74b4d/sim-swappers-phishing-verizon-sprint-tmobile-to-access-internal-tools




