.jpg?width=369&name=iStock-639646818%20(3).jpg)
With little more than some CSS and HTML coding, a security researcher demonstrates how easy it is to eliminate security warnings placed on email messages by security products.
Many organizations love the security feature where external emails are clearly marked, informing users so that anyone attempting to impersonate an internal user would raise suspicion. Hopefully, this will stop a phishing attack in its tracks.
But a clever security researcher, Louis Dion-Marcil, posted the results of his testing where he used some CSS code to simply hide the HTML-based warnings placed by a security solution.
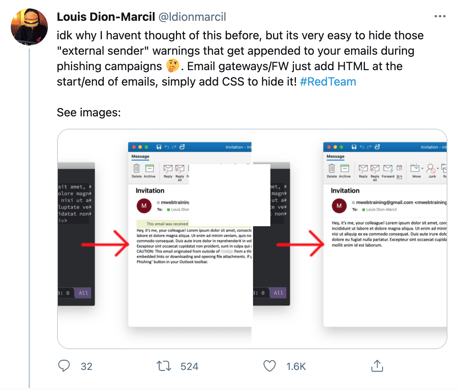
Source: Twitter
Noted in the Tweet’s comments was the fact that the HTML can just as easily be modified to indicate the email has been scanned and is legitimate.
This is very worrisome. Anytime users are asked to simply rely on technology to determine whether something is safe or is worthy of suspicion, the user tends to become complacent and blindly assumes that anything received is genuine.
However, impersonation is at an all-time high and tactics are improving each day to trick users into believing the sender is exactly they claim they are. It’s critical that users be taught using Security Awareness Training to remain vigilant, to not blindly trust security solution results. Remember, the bad guys work to evade detection by those very same products!




