 Two of the big cybersecurity attacks are the CEO Fraud (aka Business Email Compromise) which has caused $3.4 billion in damages as well as the W-2 Scams which social engineer Accounting/HR to send tax forms. Both attacks have your employees engaging and replying with the bad guys. To help inoculate employees against this type of attack we are launching a new feature: Phishing Reply Tracking (*).
Two of the big cybersecurity attacks are the CEO Fraud (aka Business Email Compromise) which has caused $3.4 billion in damages as well as the W-2 Scams which social engineer Accounting/HR to send tax forms. Both attacks have your employees engaging and replying with the bad guys. To help inoculate employees against this type of attack we are launching a new feature: Phishing Reply Tracking (*).
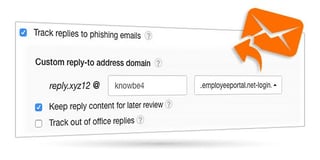
KnowBe4’s new Phishing Reply Tracking allows you to track if a user replies to a simulated phishing email and can also capture the information in the reply for review within your KnowBe4 admin console. Knowing if users are replying to phishing emails and what they are replying with is an excellent way to make sure users are following the best practices for dealing with phishing emails.
We have created a new category of system phishing templates called “Reply-To Online” which are specifically designed to test whether users will interact with “the bad guys” on the other end. However, the Phishing Reply Tracking also works with any of our existing 500+ phishing templates.
Additional options for this feature include:
- Store the reply-to content.
- Customizable reply-to address sub-domain, making the reply-to address look similar to your actual domain.
- Track out of office replies to find out if your users are including company directories and other information with their OOF messages.
Request a demo and see it in action!
Don't like to click on redirected buttons? Copy / Paste this link in your browser:
https://info.knowbe4.com/kmsat-request-a-demo
For support questions, you can review the support article at Zendesk:
https://knowbe4.zendesk.com/hc/en-us/articles/234956728-Reply-To-Phishing
(*) You need to be subscribed to the Phishing section of our service, this feature is not available if you have subscribed to Training-only.





