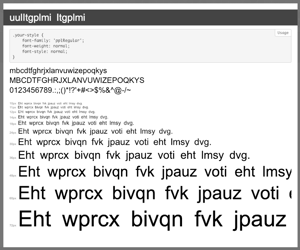
Researchers discovered a phishing template that uses a unique method for encoding text using web fonts. The researchers found that the source code of the landing page contained encoded text, but the browser unexpectedly renders it as cleartext.
The page impersonates the website of a major bank. Digging deeper, the researchers traced the source of the character substitution cipher to the page’s CSS code. The code references a “fonts” folder that doesn’t exist, so instead it loads two base64-encoded woff and woff2 font files. These font files are custom-made with the letters out of order. When the browser renders the page, it treats the font as if it’s in alphabetical order and replaces the letters in the source code with readable text.
The researchers also note that the phishing kit utilizes stolen branding to impersonate the bank, but the source code doesn’t contain the logo. Rather, the images are created via scalable vector graphics (SVG), which allows the site to evade automated scanners.
The researchers’ findings show a creative way to avoid detection by security vendors. Criminals will always find ways to bypass detection mechanisms, so organizations can’t rely solely on technical safeguards to prevent attacks. New-school security awareness training can give employees up-to-date knowledge of the various methods used by attackers to stay ahead of the curve.





