Taking advantage of the inherent trust in mobile content, the bad guys are using a mixture of phishing text messages and look-alike sites to trick users into giving up credentials.
Taking advantage of the inherent trust in mobile content, the bad guys are using a mixture of phishing text messages and look-alike sites to trick users into giving up credentials.
You get a text from “Microsoft” stating your Office 365 password has expired with a link to reset your password. You click the link and are taken to an Office 365 password reset page. Thinking nothing of it, you provide your credentials and “reset” your password. One problem – it’s all been a scam.
This is the latest technique used by cybercriminals to harvest online credentials, according to data from security firm Lookout. Because so many users utilize mobile devices for work, it’s the perfect medium to get direct access to a user without needing to fend against the traditional defenses organizations put up in front of web and email content.
According to Verizon, 51% of sophisticated threat actors are now including mobile devices in their list of target devices. And, because the credentials being sought are work-related, the mobile device attack path spells trouble for organizations.
Without an ability to properly protect corporate accounts via devices out of their control, organizations need to look to heightening the employee sense of security when interacting with anything on the Internet (regardless of device) using Security Awareness Training.
Without changing the way employees think about the complete sense of trust they have in the mobile device experience, organizations put themselves at risk of the repercussions of credential harvesting, which include ransomware attacks, data breaches, and fraud.
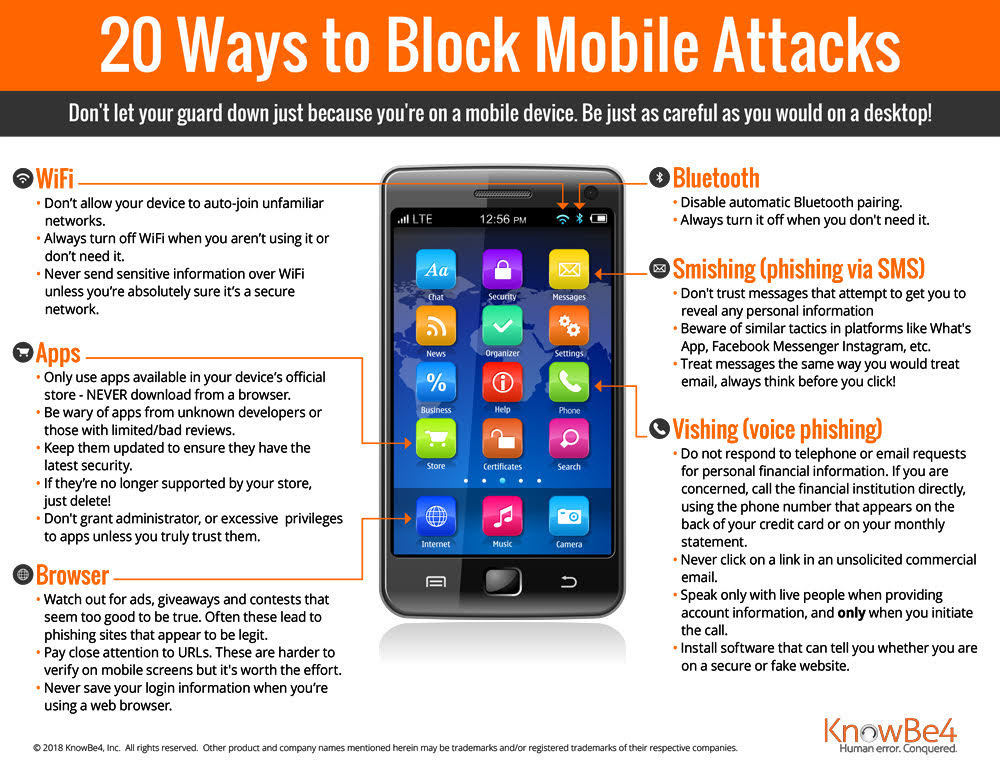
This infographic will show your users what to watch out for on mobile devices to prevent them from becoming the next victim. We recommend you print this out, full PDF here.