%20(1).jpg?width=400&name=RogerMasterClass-FeatureImage%20(1)%20(1).jpg) KnowBe4 just released its first e-book covering password attacks, defenses and what your password policy should be. Here is a summary of its recommendations:
KnowBe4 just released its first e-book covering password attacks, defenses and what your password policy should be. Here is a summary of its recommendations:
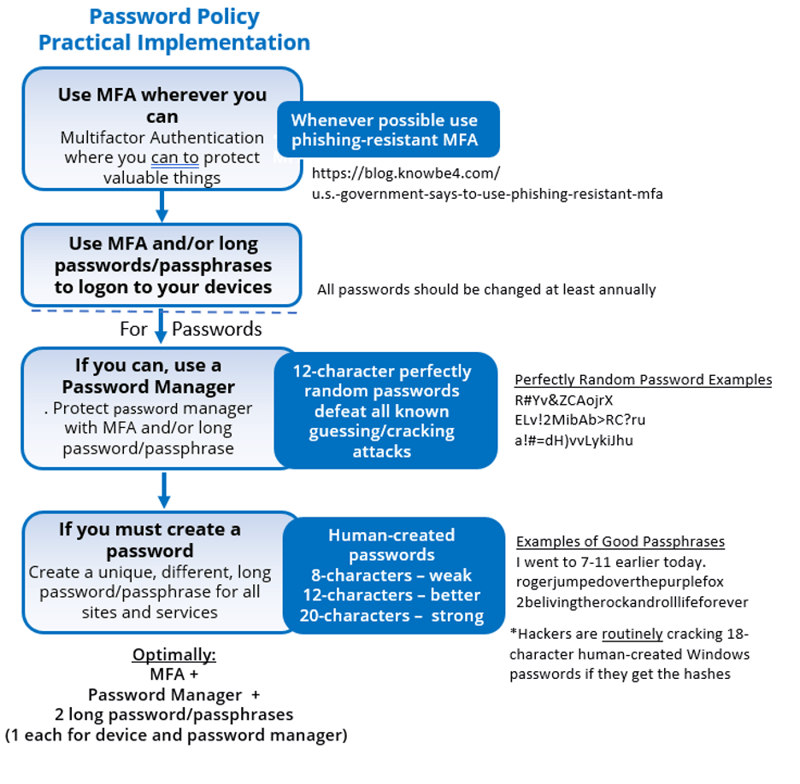
In a nutshell, KnowBe4 recommends using phishing-resistant MFA whenever you can, using a password manager to create most of your passwords, and creating 20-character or longer passwords/passphrases wherever you cannot use MFA or a password manager.
Learn more about why we recommend such long human-created passwords on the blog.
KnowBe4’s password policy white paper is the result of thousands of hours of research, lessons learned from many hundreds of hours of password hacking from legal penetration testing teams and real-world hacking scenarios. In some instances, KnowBe4’s recommendations go against another entity’s long-standing password recommendations, but we have the knowledge and experience to back up our recommendations.
The e-book covers the various types of common password attacks, including some more obscure hacking methods not usually covered by other password papers, discusses how to defend against all those attacks and then follows up with specific recommendations to defeat those attacks.
Having a secure cyber environment takes a lot more than having a great password policy and creating great passwords, but having the right passwords (and phishing-resistant MFA and using password managers) will help to significantly reduce the risk of password-based attacks.
If you have any questions or comments about KnowBe4’s new password policy paper, you can direct them to the author at: rogerg@knowbe4.com.
E-Book: What Your Password Policy Should Be
 In this e-book, Roger A. Grimes, KnowBe4’s Data-Driven Defense Evangelist, details the pros and cons of password use. Roger explains how the implementation of supporting frameworks, such as MFA and password managers, can help you keep your organization locked down.
In this e-book, Roger A. Grimes, KnowBe4’s Data-Driven Defense Evangelist, details the pros and cons of password use. Roger explains how the implementation of supporting frameworks, such as MFA and password managers, can help you keep your organization locked down.
Download this e-book to learn:
- What tactics bad actors use to hack passwords (and how to avoid them)
- The pros and cons of password managers and multi-factor authentication and how they impact your risk
- How to craft a secure password policy that addresses the most common methods of password attack
- How to empower your end users to become your best last line of defense
PS: Don't like to click on redirected buttons? Cut & Paste this link in your browser:
https://info.knowbe4.com/wp-password-policy-should-be





