
The treasurer of the city of Ottawa, Marian Simulik, fell for a business email compromise (BEC) scam and sent $100,000 to a scammer, the city’s auditor general revealed this week. Simulik received an email last July from a fraudster posing as the city manager.
The email asked her to wire the money to an IT supplier in the US. Ottawa’s website was undergoing an overhaul at the time, and Simulik assumed the request was related to this. She researched the IT supplier and conversed with the attacker via email before sending the money to a bank account in the US.
Simulik realized her error several days later, when she received another bogus request for $150,000. This email arrived when she was at a council meeting with the city manager, so she asked him personally about the request. The manager knew nothing about the matter, and Simulik told him about the money transfer that took place days earlier. Simulik was apparently mortified that she fell for the scam.
"That I should be the target and victim of this sophisticated attack has affected me deeply both professionally and personally," she said.
Ottawa’s auditor general also revealed that the treasurer’s office had been targeted by a different BEC attack several months earlier, when an email purporting to come from the CEO of the city’s public library requested a money transfer. This incident was identified as a scam before any money was sent, but treasury staff failed to report the event to security personnel.
In response to these incidents, the city has implemented measures to prevent the same employee from creating and approving a money transfer. It also plans to require mandatory awareness training for city employees. New-school security awareness training can help your employees identify these scams by confirming that emails are legitimate before acting on them. CBC has the story: https://www.cbc.ca/news/canada/ottawa/city-treasurer-sent-100k-to-fraudster-1.5088744
How many of your users would reply to a spoofed email?
 KnowBe4’s Phishing Reply Test (PRT) is a new and complimentary IT security tool that makes it easy for you to check to see if key users in your organization will reply to a highly targeted impersonation attack. You’ll get quick insights into how many users will take the bait so you can take action to train your users and better protect your organization from these fraudulent attacks!
KnowBe4’s Phishing Reply Test (PRT) is a new and complimentary IT security tool that makes it easy for you to check to see if key users in your organization will reply to a highly targeted impersonation attack. You’ll get quick insights into how many users will take the bait so you can take action to train your users and better protect your organization from these fraudulent attacks!Here’s How the Phishing Reply Test works:
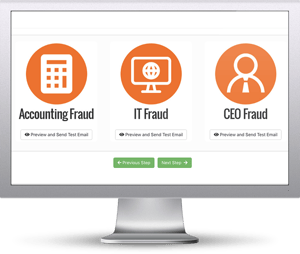
- Immediately start your test with your choice of three phishing email reply scenarios
- Spoof a Sender’s name and email address your users know and trust
- Phishes for user replies and returns the results to you
- Get a PDF emailed to you within 24 hours with the percentage of users that replied
Identify how many of your users take the bait...and reply to a spoofed email before the bad guys do!
Don't like to click on redirected buttons? Copy & paste this link into your browser:





