 Attackers stole millions of dollars from Oklahoma’s pension fund for retired law enforcement officers, the Oklahoman reports. The Oklahoma Law Enforcement Retirement System (OLERS) said the funds were stolen on August 26th, after an employee’s email account was hacked. The attackers were able to divert $4.2 million being handled by an investment manager.
Attackers stole millions of dollars from Oklahoma’s pension fund for retired law enforcement officers, the Oklahoman reports. The Oklahoma Law Enforcement Retirement System (OLERS) said the funds were stolen on August 26th, after an employee’s email account was hacked. The attackers were able to divert $4.2 million being handled by an investment manager.
The FBI has recovered $477,000 of the stolen funds, and OLERS believes they’ll be able to recover more. Otherwise, the agency’s insurance provider will have to make up the losses.
The employee whose account was hacked wasn’t fired, and OLERS is providing employee training to prevent this type of attack in the future. OLERS’ president, Roy Rogers, told the Oklahoman that business email compromise can affect anyone.
“It happens every day,” Rogers said. “It can happen to an individual. It can happen to a state. It can happen to a company....This kind of crime has just got rampant.”
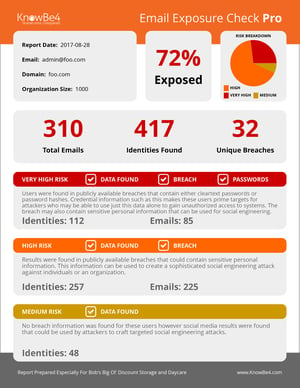
Technical defenses alone aren’t enough to thwart social engineering attacks. Security controls like two-factor authentication are essential, but even these can be defeated by a determined attacker who targets the human. New-school security awareness training can address human vulnerabilities and turn your employees into security assets.
The Oklahoman has the story: https://oklahoman.com/article/5640503/hackers-get-42-million-from-pension-fund-for-retired-troopers-state-agents
 Here's how it works:
Here's how it works:




