 The use of employees as insider accomplices potentially changes how social engineering is being used in exchange for a direct request for internal assistance.
The use of employees as insider accomplices potentially changes how social engineering is being used in exchange for a direct request for internal assistance.
Security researchers at Abnormal Security have identified a recent set of emails soliciting employees of a would-be victim organization to participate in helping the threat actors by installing DemonWare/Black Kingdom ransomware within the organization.
The emails are simple in nature and contain no malicious links or attachments – something the threat actors hope will allow their request to get past security solutions.
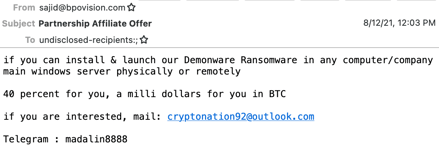
Source: Abnormal Security
The researchers at Abnormal Security decided to engage the threat actors to better understand how the infection would take place. A link to an executable file was provided via file sharing sites WeTransfer or Mega.nz. It’s also interesting to note that the $1M purse offered in the initial email was dropped down (during Abnormal Security engaging of the threat actor) to an offer of only $120K.
What’s most interesting is that Abnormal Security was able to get the threat actor to tell them his source of contacts: CEO and CFO emails from LinkedIn. So, even this lone threat actor is doing proper diligence using whatever means they can to target individuals within an organization.
While it’s evident this type of attack doesn’t fall within the realm of phishing, it could have gone awry in more ways than one. In this specific instance, the attacker legitimately wanted the insider to do all the work. But it’s also conceivable that social engineering could have been used to compromise credentials along the way. So it’s still important to include Security Awareness Training of even your highest C-level executives to ensure they don’t fall prey to scams.
 Here's how it works:
Here's how it works:




