 The FBI calls CEO Fraud "Business Email Compromise" (BEC) and it has become a highly lucrative threat vector for attackers. According to IC3, the FBI's Internet Crime Complaint Center, 5.3 billion dollars was stolen due to BEC fraud between October 2013 and December 2016. In comparison, ransomware exploits took in 1 billion dollars in 2016.
The FBI calls CEO Fraud "Business Email Compromise" (BEC) and it has become a highly lucrative threat vector for attackers. According to IC3, the FBI's Internet Crime Complaint Center, 5.3 billion dollars was stolen due to BEC fraud between October 2013 and December 2016. In comparison, ransomware exploits took in 1 billion dollars in 2016.
Recently FlashPoint uncovered a BEC that is thought to be operating out of West Africa. This isn’t your typical “Nigerian” email spam scam informing you that Barrister Jones has USD 20,000,000 waiting for you in an escrow account.
Based on the IP addresses gathered by Flashpoint, this is a highly organized phishing scam operation based out of Nigeria attempting to steal the business email credentials of users across a broad spectrum of industries. They hope to compromise their accounts and leverage them for even more targeted spear phishing scams, researchers at Flashpoint reported.
Yet this simple scam seems to be doing a good job at evading detection. It uses a well-known method of sending the user an email with a PDF file embedded with a redirection link to phony sites especially created to grab credentials. Unlike old-time scammers who used a shotgun approach, these attacks are very targeted.
In the scope are universities, software, and technology companies, retailers, engineering and real estate firms…and even churches. Good "credential-attacks" require very good mimicry of trusted entities in their email communications and phony sites to gain the trust of the victims. So these scammers seem to have moved up the food chain and "gotten their BEC diplomas".
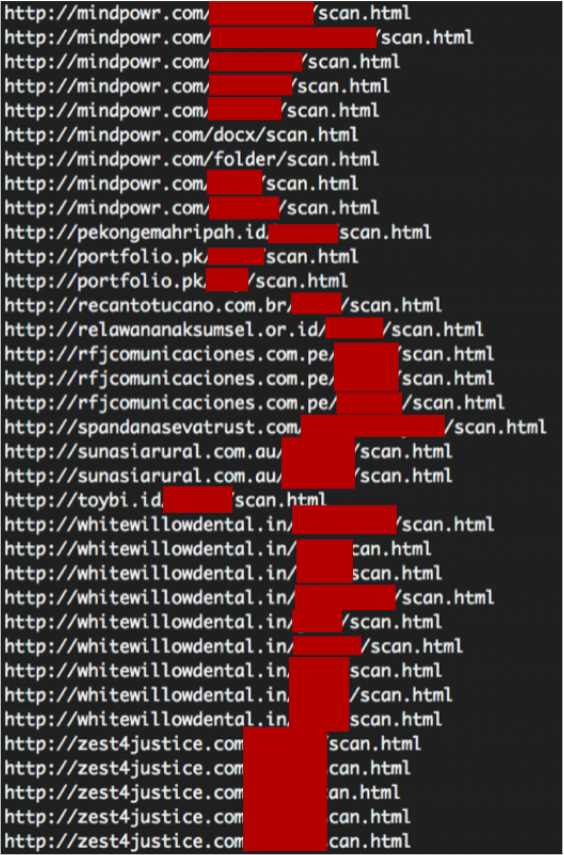
Flashpoint researchers looked at 73 files sent during a period from March 28 through August 8, 2017, and found seventy unique Uniform Resource Identifiers (URIs); with many using the same domains. This is one of the findings that led to the conclusion that this ring was based in and highly likely operating out of Nigeria.
• The attack follows the basic redirect and credential stealing techniques.
• The victim receives a PDF email attachment with a malicious link.
• Upon opening the PDF, the victim is redirected to open a secure document.

Upon opening the document, the victim is redirected to a phony but fairly well simulated well-known site such as a fake Office 365 portal and is then instructed to log in using their user id and password credentials.
If the user successfully takes the bait and provides his or her real credentials, the scammers quickly start working behind the scene and begin the next phase of the attack by grabbing his or her contact list. They now have trusted contact email addresses -- which might already be whitelisted across the org and org partners.
This sets up not only the organization being attacked but also assists in targeting other organizations doing business with the comprised organization. Meanwhile, the scammers can be off the radar or they can continue to harvest more contacts to continue the scam across organizations.
“Flashpoint analysts concluded that these attacks are likely Nigerian due to the originating IP addresses of the phishing emails, as well as the actors’ tactics, techniques, and procedures (TTPs), such as the focus on credential phishing, the absence of malware, and a lack of operations security (OPSEC) practices on the attackers’ part.”
Now here’s the astounding part of the story...
“While BEC actors operating out of western Africa are broadly considered among the lowest-skilled cyber threat actors, they have been responsible for more than $5 billion USD in fraud in the last three years. In comparison, ransomware was projected to be a $1 billion USD industry in 2016, and Europol estimated that the now-defunct AlphaBay Market was responsible for almost $1 billion USD in business between its creation in 2014 and its closure in July 2017.”
“BEC actors and cybercriminals located in West Africa typically do not make significant efforts to enhance their OPSEC practices or conceal their locations; however, they are still largely successful in stealing billions of dollars from publicly traded and high-profile organizations each year.” Source: https://www.flashpoint-intel.com/blog/bec-credential-phishing/
CEO Fraud Prevention Manual Download
CEO fraud has ruined the careers of many executives and loyal employees. Don’t be next victim. This brand-new manual provides a thorough overview of how executives are compromised, how to prevent such an attack and what to do if you become a victim.
PS: Don't like to click on redirected buttons? Copy and paste this link in your browser:





