
Lucian Constantin at CSO had the scoop. A new ransomware program written in Windows PowerShell is being used in attacks against enterprises, including health care organizations, researchers warn. The initial ransom is ~$500, but it goes up to ~$1,000 after a couple of weeks.
PowerShell is a task automation and configuration management framework that's included in Windows and is commonly used by systems administrators. It has its own powerful scripting language that has been used to create sophisticated malware in the past.
The new ransomware program, dubbed PowerWare, was discovered by researchers from security firm Carbon Black and is being distributed to victims via spear phishing emails containing Word documents with malicious macros, an increasingly common attack technique. Something new here not typically seen in a widespread campaign is the emails use the victims names and information about their companies.
What sets PowerWare apart from other crypto-ransomware samples is that it is fileless, which is a tactic adopted by other malware families pushed in prolific exploit kits such as Angler. Palo Alto Networks, for example, disclosed on March 11 a malware family called PowerSniff that has similar behaviors to PowerWare, including fileless infections.
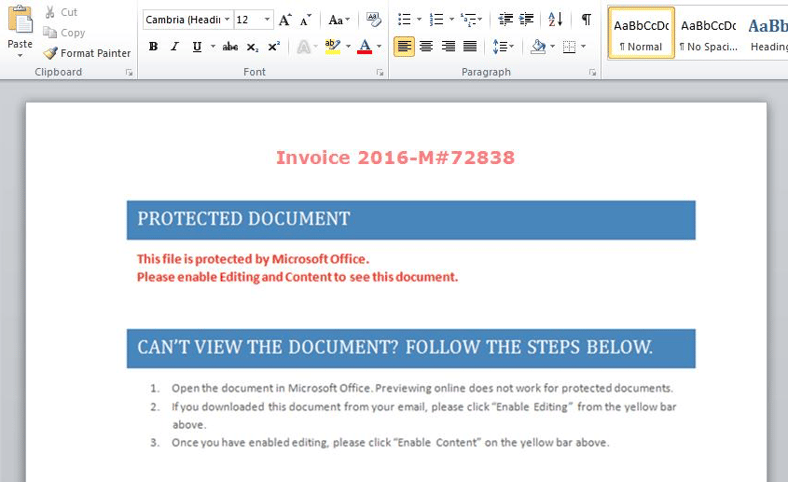
In this example, if the user enables the macros to run, cmd.exe will be spawned to launch a pair of instances of PowerShell: one that downloads the ransomware script and another that starts PowerShell with the script as input.
According to research by Palo Alto networks, the script runs a series of checks on the computer with the goal of finding systems used to conduct financial transactions and to avoid security researchers as well as medical and educational institutions.
This is not the first time that PowerShell is used to create malware, While PowerShell-based malware is not new, its use has increased in recent months and it is arguably harder to detect than traditional malware because of PowerShell's legitimate use and popularity, especially in enterprise environments.
Check the Maktub Locker ransomware posts for some great suggestions how to stop these kinds of attacks.
Download Your Ransomware Hostage Rescue Manual
Get the most complete (updated spring 2016) Ransomware Manual packed with actionable info that you need to have to prevent infections, and what to do when you are hit with ransomware.
If you do not like to click on buttons with redirects, cut/paste this link in your browser:





