 Researchers at HuntressLabs “@Huntress” uploaded a YouTube video and commentary on their Twitter account that demonstrates a new variant of Ragnar Locker /Ragnar Locker Ransomware that uses a stealthy technique to evade MSP detection prior to encryption. Ragnar Locker scans the running process and services and terminates the processes of many popular MSP RMM (Remote Monitoring and Management) admin tools. Hunt and kill processes technique have been used by ransomware groups before such as Clop, Nemty, Robinhood, Ekans and others. But this new variant uses this approach to go after networks and data in the Cloud.
Researchers at HuntressLabs “@Huntress” uploaded a YouTube video and commentary on their Twitter account that demonstrates a new variant of Ragnar Locker /Ragnar Locker Ransomware that uses a stealthy technique to evade MSP detection prior to encryption. Ragnar Locker scans the running process and services and terminates the processes of many popular MSP RMM (Remote Monitoring and Management) admin tools. Hunt and kill processes technique have been used by ransomware groups before such as Clop, Nemty, Robinhood, Ekans and others. But this new variant uses this approach to go after networks and data in the Cloud.
Ransomware groups would love to get a foothold inside an MSP because it provides a much more efficient means to get to many more targets if they can push ransomware to their clients. These attacks are known as MSP downstream attacks.
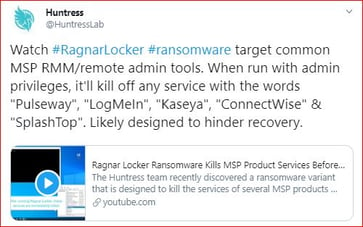
According to Huntress, “when running with admin privileges, it'll kill off any service with the words "Pulseway," "LogMeIn," "Kaseya," "ConnectWise" & "SplashTop." Likely designed to hinder recovery.”
Once these RMM processes are killed off, Ragnar Locker hopes to stay undetected by the managed service providers while they encrypt the data.
Ragnar Locker also appears to or at least implies that it's first scanning and exfiltrating sensitive and confidential information before the encryption process runs just in case the victim has second thoughts about paying the ransom. That is disclosed in the ransom note.
The Ragnar Ransomware variant leaves the usual ransomware message, BUT like many other ransomware groups jumping on the Ransomware 2.0 train, they inform the victim that they’ve scanned your network, stolen sensitive or confidential data and will make it public or sell it to a re-seller if a victim doesn’t comply with their terms. In other words pay us one way or another.
Example section of the extortion note
Source: @Huntress
***********How much time you have to pay?**********
- You should get in contact with us within 2 days after you noticed the encryption to get a better price.
- The price would be increased by 100% (double price) after 14 Days if there is no contact made.
- The key would be completely erased in 21 day if there is no contact made or no deal made.
Some sensitive information stolen from the file servers would be uploaded in public or to re-seller.
Ransomware groups are constantly innovating, evolving. and adapting to take advantage of undiscovered and unknown weaknesses in the defensive walls and hacking the human. Stay vigilant, keep up your defense in depth and train your humans with New School Security Awareness Training. Ransomware is going nuclear, stealing data and threatening to go public! Don't get caught in the fallout. Watch our webinar!




