 The Ransomware Task Force, a public-party coalition of more than 50 experts, has shared a framework of actions to disrupt the ransomware business model.
The Ransomware Task Force, a public-party coalition of more than 50 experts, has shared a framework of actions to disrupt the ransomware business model.
One of the priority recommendations refers to better regulating the cryptocurrency sector, which plays an essential part in obfuscating the threat actors and making ransomware attacks a lucrative endeavor.
Priority actions
In a document released today, the Institute for Security and Technology (IST) provides a list of 48 actions that governments and leaders in the private sector can adopt to seriously curb the ransomware threat.
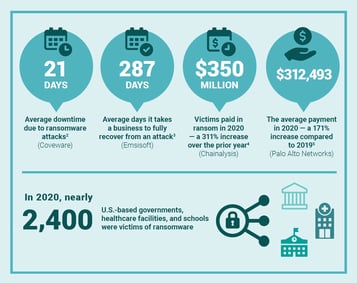
Ransomware activity has grown constantly over the past years as cybercriminals increased their attacks to targets in both the private and the public sector (including healthcare and education branches).
Priority recommendations:
- Coordinated international diplomatic and law enforcement efforts must proactively prioritize ransomware through a comprehensive, resourced strategy, including using a carrot-and-stick approach to direct nation-states away from providing safe havens to ransomware criminals
- The United States should lead by example and execute a sustained, aggressive, whole of government, intelligence-driven anti-ransomware campaign, coordinated by the White House. In the U.S., this must include the establishment of 1) an Interagency Working Group led by the National Security Council in coordination with the nascent National Cyber Director; 2) an internal U.S. Government Joint Ransomware Task Force; and 3) a collaborative, private industry-led informal Ransomware Threat Focus Hub.
- Governments should establish Cyber Response and Recovery Funds to support ransomware response and other cybersecurity activities; mandate that organizations report ransom payments; and require organizations to consider alternatives before making payments.
- An internationally coordinated effort should be developed to develop a clear, accessible, and broadly adopted framework to help organizations prepare for, and respond to, ransomware attacks. In some under-resourced and more critical sectors, incentives (such as fine relief and funding) or regulation may be required to drive adoption.
- The cryptocurrency sector that enables ransomware crime should be more closely regulated. Governments should require cryptocurrency exchanges, crypto kiosks, and over-the-counter (OTC) trading “desks” to comply with existing laws, including Know Your Customer (KYC), Anti-Money Laundering (AML), and Combatting Financing of Terrorism (CFT) laws.
Congress help needed
Some of the rules developed within the Ransomware Task Force (RTF) require Congressional help to modernize some cybersecurity laws, such as the Cybersecurity Information Sharing Act of 2015 and the Computer Fraud and Abuse Act (CFAA).
The changes should incentivize ransomware victims to share anonymously ransomware payment details (cryptocurrency wallet addresses, transaction hashes, ransom notes).
They should also allow a broader set of actions to parties dealing with a ransomware incident “when acting in good faith without fear of legal liability.”
“The strategic framework is organized around four primary goals: to deter ransomware attacks through a nationally and internationally coordinated, comprehensive strategy; to disrupt the business model and reduce criminal profits; to help organizations prepare for ransomware attacks; and to respond to ransomware attacks more effectively” - Ransomware Task Force
RTF's recommendations are designed for long-term effect once adopted and are likely to improve the cybersecurity posture of organizations. They can also tighten the collaboration between multiple actors dedicated to keeping the world safe from cyber threats.
 Here's how it's done:
Here's how it's done:




