Purporting to be invoices and payment reminders, this new campaign targets users of the popular accounting software to install the banking trojan on its victims endpoints.
Purporting to be invoices and payment reminders, this new campaign targets users of the popular accounting software to install the banking trojan on its victims endpoints.
The bad guys have long known that emails involving the concept that the recipient owes money will get a response. They also know if you use a product or service that many people have already, you’ll equally get a response. Put them together and you have phishing magic.
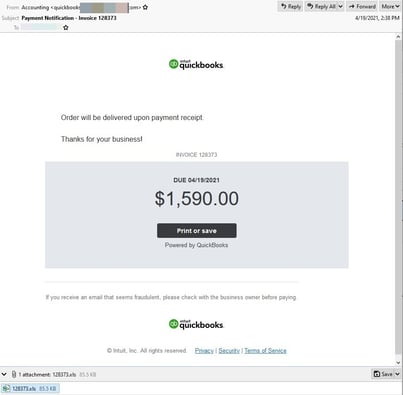
That’s what security researchers at Bitdefender are seeing with this latest campaign of attacks on users of QuickBooks. Emails informing recipients of sizable amounts of money due is all it takes to get the click from the user:
Source: Bitdefender
The goal is to infect the victim endpoint with Dridex – a banking Trojan designed to steal banking credentials and other confidential information that can be used to access bank accounts and make fraudulent transactions. Dridex is commonly delivered via phishing emails that use malicious Microsoft Word and Excel documents as attachments.
The bad news is that the preponderance of smaller companies using QuickBooks makes this phish theming cast a pretty large net. Even if the recipient isn’t in Accounting or Finance, they may still wonder why does QuickBooks think the victim organization owes them a material amount of money.
This attack is pretty brilliant. So, you need to educate your users via Security Awareness Training to avoid this and other scams like it. Remember, with Dridex the end result could be a completely wiped out bank account, so taking the time to educate users will result in a valuable ROI.