.jpg?width=300&name=iStock-1184072557%20(1).jpg) One of the most dangerous pieces of malware is back with a new campaign that takes advantage of social engineering techniques to look convincing enough to fool your users.
One of the most dangerous pieces of malware is back with a new campaign that takes advantage of social engineering techniques to look convincing enough to fool your users.
The last thing you want to hear when you ask “so what malware hit us?” is “Qbot. This is really nasty malware that steals just about everything off of the infected computer and can leave the door open for attackers to come back into your network whenever they want.
A newly spotted campaign uses some pretty convincing use of graphics and impersonation of Microsoft’s Windows Defender to trick victims into enabling an email attachment used as the initial dropper.
Traditionally, phishing campaigns involving Qbot revolve around invoices, payment documents, and other financial-related concerns. Excel (.xlsx) files are typically used as the attachment to take advantage of the well-used macros functionality built into Office applications.
What makes this attack so interesting is the contents of the Excel document. The bad guys need the victim to enable macros, and (we hope) users won’t normally fall for this. But this latest attack uses a well-thought out presentation to convince the user it’s ok to enable macros:
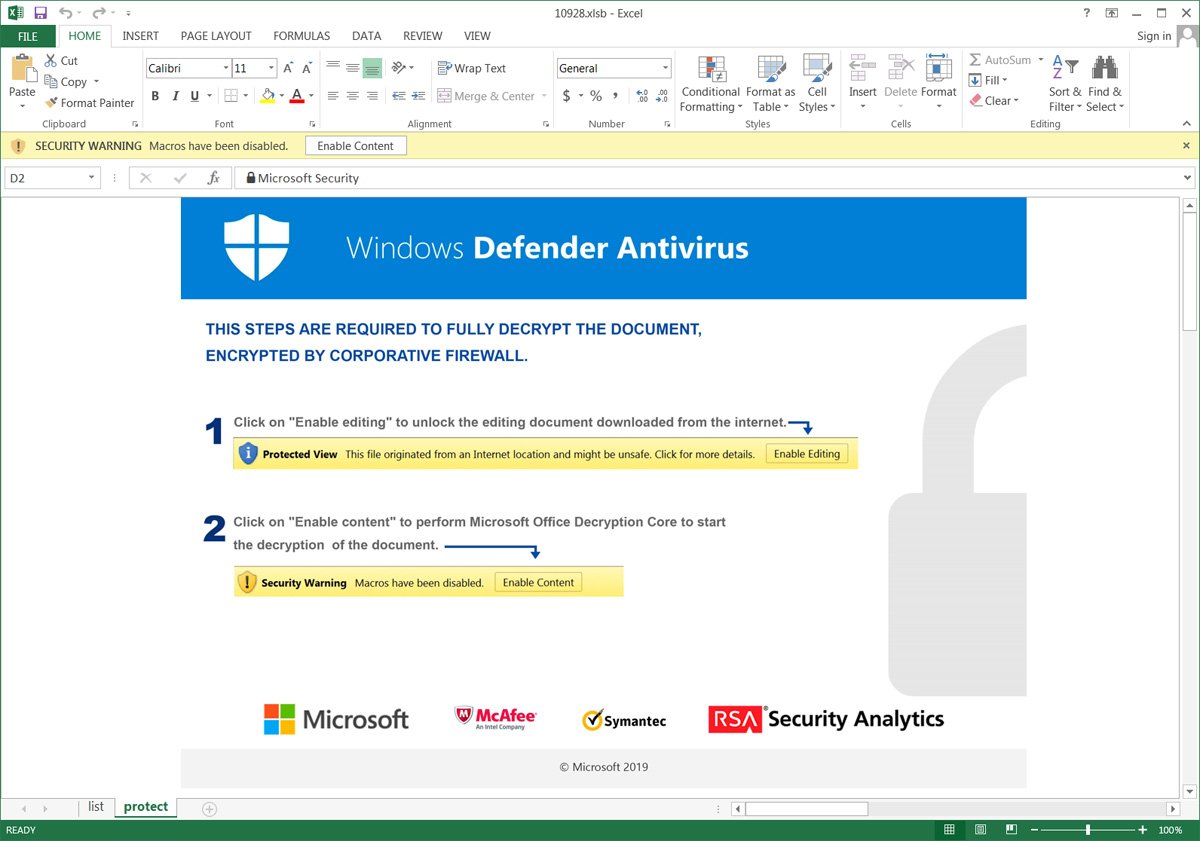
Pretending to be Windows Defender and using some security vendor logos to help establish credibility that it's "ok" to enable macros, Qbot has a very good chance of successfully fooling the unsuspecting user.
And once macros are enabled, it’s game over.
Users need to be taught via Security Awareness Training that Office documents with attachments should never have macros enabled (unless the user operates in a business function where macros are needed, in which case, every email should be opened with a dose of suspicion).




