 This banking trojan-turned-information-stealer has been around for nearly 15 years. But its latest iteration – seen even in the past few weeks – has stepped up in its’ ability to act quickly.
This banking trojan-turned-information-stealer has been around for nearly 15 years. But its latest iteration – seen even in the past few weeks – has stepped up in its’ ability to act quickly.
A few months back I wrote about SnapMC – a cybercriminal group that focuses on data theft and extorting payment to not publish the data. This group is able to gain access and steal data within 30 minutes. At the time this was unheard of; the average ransomware dwell time (from initial attack to launch of the ransomware) was measured in days (and still is today).
But now we’re hearing about more attacks that are taking less than an hour. In this latest attack using QBot, the security researchers at The DFIR Report document a speedy attack model they first saw in October of last year that they state they are continuing to see today.
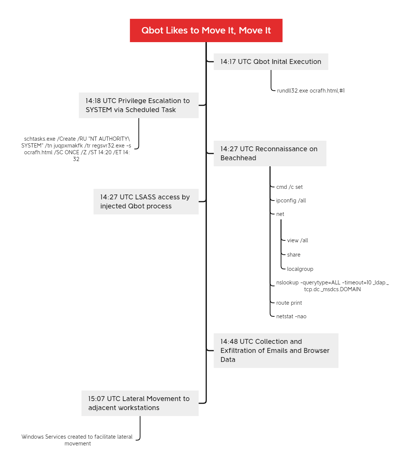
Qbot leverages a mix of HTML scripting, the Windows Task Scheduler service, reconnaissance using built-in Windows tools, and access to the Local Security Authority Server Service (LSASS) to gain control over an endpoint.
The article is helpful enough to also provide a timeline of the actions taken:
Source: DFIR Report
The scariest part of this is noted in the article:
“Thirty minutes after initial access, Qbot was observed collecting data from the beachhead host including browser data and emails from Outlook.”
According to the DFIR Report analysts, the QBot-based attacks were delivered via phishing campaign with a malicious Excel attachment. This puts the onus on the recipient user to engage with the attachment in the first place – something Security Awareness Training would teach them not to do.
If this keeps up 30 minutes will be the new standard for how long organization Security has to detect the threat actor. But if you can engage your users to be vigilant, the “threat timer”, as it were, will never get started.
 Here's how it works:
Here's how it works:




