 A new PhaaS service brings the power of bypassing multi-factor authentication (MFA) to the world’s most-used email platforms.
A new PhaaS service brings the power of bypassing multi-factor authentication (MFA) to the world’s most-used email platforms.
At its core, Tycoon 2FA isn’t doing anything new. It uses a reverse proxy server to host a phishing web page that impersonates the legitimate email platform in question. Then it intercepts the victim's input and relays them to the legitimate service.
But it’s how this platform does it that is sophisticated. In a deep dive analysis of the phishing kit by security vendor Sekoia, we get a glimpse into just how sophisticated and much work goes into this latest iteration of the PhaaS platform.
Check out the following diagram and to understand how it bypasses 2FA without letting the victim know.
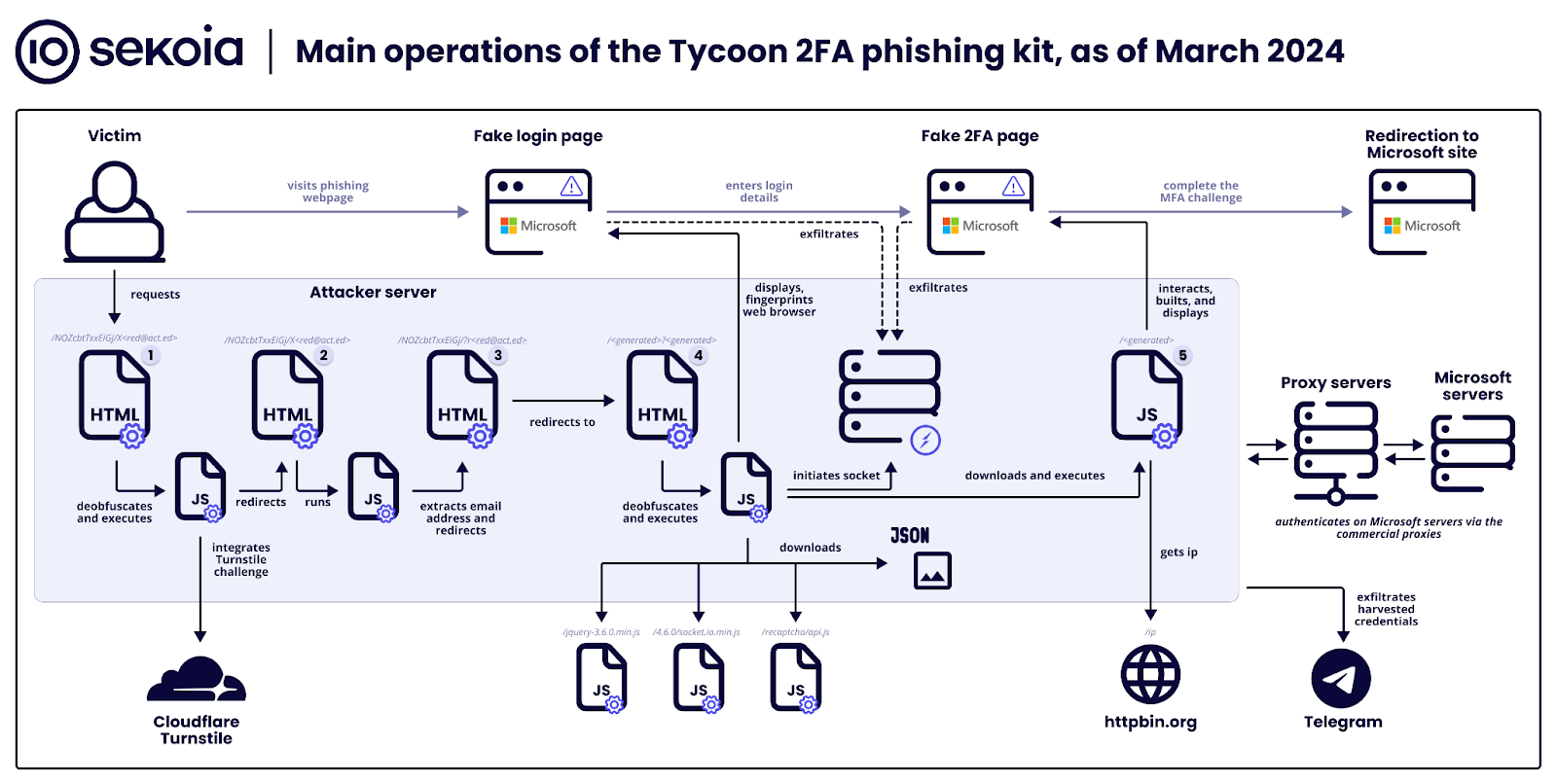
Source: Sekoia
According to Bleeping Computer’s coverage of the Sekoia analysis, there are seven stages in this attack:
- Stage 0 – Attackers distribute malicious links via emails with embedded URLs or QR codes, tricking victims into accessing phishing pages.
- Stage 1 – A security challenge (Cloudflare Turnstile) filters out bots, allowing only human interactions to proceed to the deceptive phishing site.
- Stage 2 – Background scripts extract the victim's email from the URL to customize the phishing attack.
- Stage 3 – Users are quietly redirected to another part of the phishing site, moving them closer to the fake login page.
- Stage 4 – This stage presents a fake Microsoft login page to steal credentials, using WebSockets for data exfiltration.
- Stage 5 – The kit mimics a 2FA challenge, intercepting the 2FA token or response to bypass security measures.
- Stage 6 – Finally, victims are directed to a legitimate-looking page, obscuring the phishing attack success.
According to Sekoia, Tycoon has received an estimated total of over $394K in bitcoin since the services inception back in 2019. Sekoia estimate that “several hundred Tycoon 2FA kits were sold as-a-service over half a year” since the latter part of 2024, demonstrating that this phishing kit is growing in popularity and effectiveness.
KnowBe4 empowers your workforce to make smarter security decisions every day. Over 65,000 organizations worldwide trust the KnowBe4 platform to strengthen their security culture and reduce human risk.






