Security researchers have discovered a cunning PDF-based phishing attack that leverages social engineering and PDF prompt specifics to trick users into opening malicious Office docs.
Security researchers have discovered a cunning PDF-based phishing attack that leverages social engineering and PDF prompt specifics to trick users into opening malicious Office docs.
At this point, every organization should already know that any kind of Office doc sent as an attachment from someone you don’t know should automatically be assumed to be malicious in nature. But a new attack, discovered by HP Wolf Security, embeds a Word doc within a PDF and uses some social engineering to trick users into thinking the embedded file is safe.
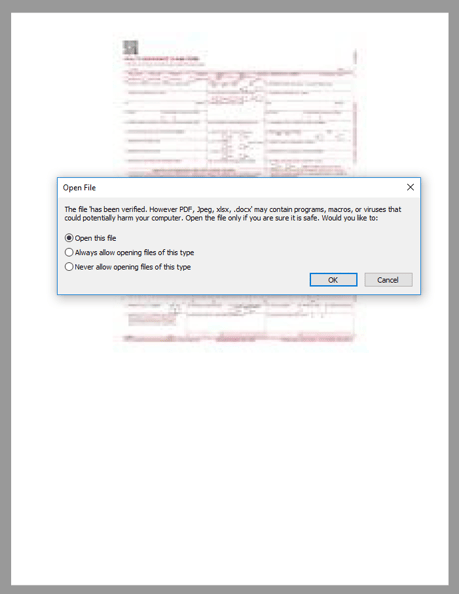
According to the analysis of the attack, an email with the attachment “REMMITANCE INVOICE.pdf” is sent. Should the file be opened, the victim recipient is immediately asked to open an embedded Word doc, but is prompted with details that make it seem like the file is safe:
Source: HP Wolf Security
Note the filename – it’s “has been verified. However PDF, Jpeg, xlsx, .docx” Seems a bit odd – that is until you read the filename in the context of the PDF open warning – it’s designed to make it sound to the user that the file has been determined to be safe. (Go back and read the prompt above again and you’ll see how sneakily this document name is inserted into the dialog box message).
After a series of steps that take into account whether Protected View is enabled or not, the attack eventually installs Snake Keylogger malware.
The point at which this attack should be spotted for what it really is, is at the point when the user receives the email. Are you expecting an invoice? Do you know the person the email is sent from? Does the email address match the company the invoice purports to be from?
All these questions are commonplace for users who has undergone continual Security Awareness Training that teaches users what to look for and how to identify suspicious – if not downright malicious – email content which would cause even the sneaky campaign above to fail before it ever got a chance to start.