 In yet another case of brand impersonation, this new phishing scam seeks out the millions of LifeLock customers and follows a seasoned infection path, with the goal being persistence and control.
In yet another case of brand impersonation, this new phishing scam seeks out the millions of LifeLock customers and follows a seasoned infection path, with the goal being persistence and control.
Security researchers at Palo Alto Network’s Unit 42 division have identified a new scam in the wild. Sent to potential victims posing as Norton LifeLock, the email indicates that the email includes a password-protected Word Document containing a secure personal message that requires macros be enabled.
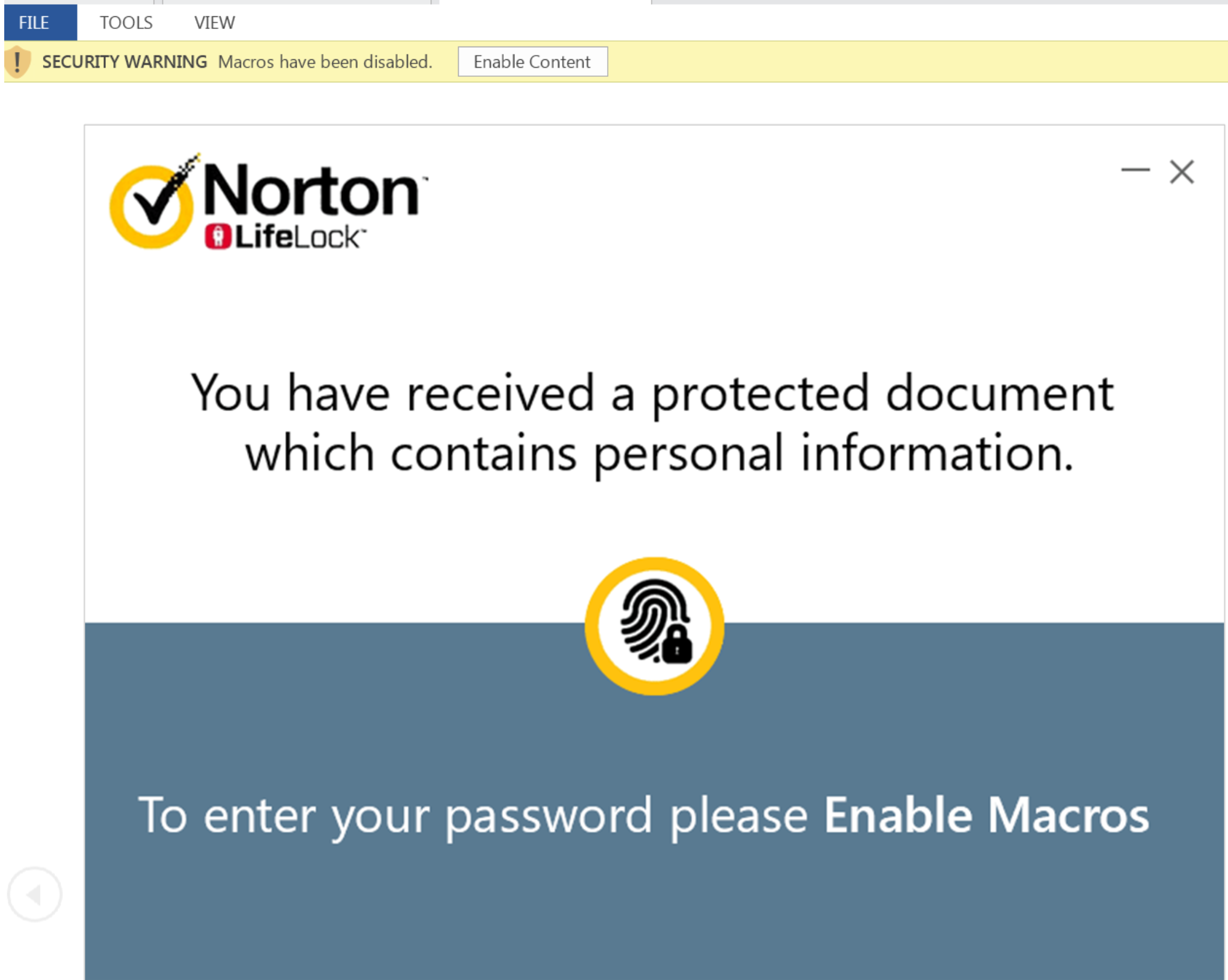
Once the user enables macros and enters in a confirmation password of the letter ‘C’, the embedded macro takes over. Utilizing Windows tools including CMD and MSIexec, the infection results in the installation of NetSupport Manager, a legitimate remote control software.
Persistence is achieved by saving a PowerShell script on the user’s %temp% folder and configuring the registry to ensure the script is run each time the system boots.
The ramifications of this are endless – access to corporate endpoints, installing keyloggers and waiting for the right set of credentials to facilitate lateral movement, monitoring of financial transactions, and more.
This attack obviously is of a personal nature – it’s important that users be educated through Security Awareness Training to be cognizant of the implications to the organizations should an email turn out to be a cyberattack and, therefore, work with a vigilant mindset. Users that undergo this training to be security conscious are 87.5% less likely to fall for a phishing scam like this.
Today it’s Norton LifeLock. Tomorrow it will be another impersonated brand. The trick here is to prepare for all of these attacks and not just respond to this one only.




