Spam distributors are using a new technique to infect users with malware, and while this phishing attack relies on having users open Word documents, it does not involve social engineering users to enable macro scripts.
This new macro-less technique is currently under active exploitation, being detected by Trustwave SpiderLabs researchers in an ongoing malware campaign.
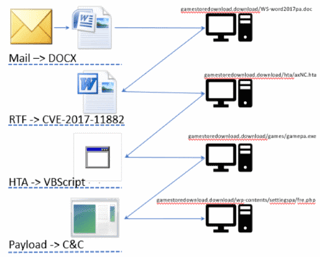
New technique's exploitation chain
The actual exploitation chain is detailed below and relies on a large number of resources, such as DOCX, RTF, HTA, VBScript, and PowerShell.
⏩ A victim receives a spam email with a DOCX file attachment.
⏩ Victim downloads and opens the DOCX file.
⏩ DOCX file contains an embedded OLE object.
⏩ OLE object downloads and opens an RTF (disguised as a DOC) file.
⏩ DOC file uses CVE-2017-11882 Office Equation Editor vulnerability.
⏩ Exploit code runs an MSHTA command line.
⏩ MSHTA command line downloads and runs an HTA file.
⏩ HTA file contains a VBScript that unpacks a PowerShell script.
⏩ PowerShell script downloads and installs the password stealer.
⏩ Malware steals passwords from browsers, email and FTP clients.
⏩ Malware uploads data to a remote server.
The technical details of this attack are at: https://www.bleepingcomputer.com/news/security/multi-stage-word-attack-infects-users-without-using-macros/
Do your users know what to do when they receive a suspicious email?
Should they call the help desk, or forward it? Should they forward to IT including all headers? Delete and not report it, forfeiting a possible early warning?

KnowBe4’s Phish Alert button now also works for Gmail users with G Suite using Chrome. This gives your users a safe way to forward email threats to the security team for analysis and deletes the email from the user's inbox to prevent future exposure. All with just one click!
Best of all, there is no charge!
- Reinforces your organization's security culture
- Incident Response gets early phishing alerts from users, creating a network of “sensors”
- Email is deleted from the user's inbox to prevent future exposure
- Easy deployment via MSI file for Outlook, G Suite deployment for Gmail (Chrome)
- Supports: Outlook 2007, 2010, 2013, 2016 & Outlook for Office 365, Exchange 2013 & 2016, Chrome 54 and later (Linux, OS X and Windows)
This is a great way to better manage the problem of social engineering. Compliments of KnowBe4!
If you do not like to click on buttons with redirects, here is a link you can cut and paste into your browser: https://info.knowbe4.




