 The cybercriminal gang, dubbed ‘Luna Moth’ uses a sophisticated mix of phishing, vishing, remote support sessions, and remote access trojans to gain control of victim endpoints.
The cybercriminal gang, dubbed ‘Luna Moth’ uses a sophisticated mix of phishing, vishing, remote support sessions, and remote access trojans to gain control of victim endpoints.
This latest attack example comes to us via the security researchers at security vendor Sygnia. Last month, they documented a series of phishing attacks by a ransom group they’ve named ‘Luna Moth’. This gang focuses on exfiltrating data and extorting a ransom from the victim, threatening to publish the data.
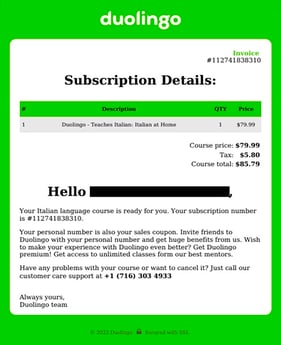
The phishing attack uses a few different methods to both get the attention of, and throw off, the potential victim. It starts with an email sent to the victim using a from address of the victim’s “first.last” name, prepended to either “.zohomasterclass@gmail.com” or “.duolingo@gmail.com”.
The email content makes the assumption the victim has signed up for a subscription, and provides an invoice on which is a phone number to call to dispute the invoice.
Source: Sygnia
The victim is directed to join a Zoho remote support session, install the Zoho Assist application, and is eventually tricked into downloading and installing a legitimate remote administration tool that gives the threat actor access.
There are a ton of red flags that users in your organization should spot immediately. First off, no legitimate company makes you jump through so many hoops to cancel a subscription. Second, the sender email is completely unrealistic, and install software as part of cancelling a subscription??? C’mon.
And yet, unsuspecting victims fall for this. That’s why Security Awareness Training is so necessary. Users need to understand and be familiar with the malicious tactics used so they can err on the side of caution, rather than begin with the premise that an email like the one above is legitimate.




