 Leveraging Microsoft Exchange’s Basic Authentication support, scammers were able to use harvested online credentials and bypass any MFA in place, giving them access to mailboxes.
Leveraging Microsoft Exchange’s Basic Authentication support, scammers were able to use harvested online credentials and bypass any MFA in place, giving them access to mailboxes.
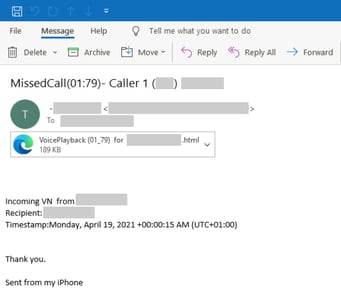
A new attack identified by Microsoft begins with a simple phishing campaign touting a file the recipient must read pointing to a malicious link that takes victims to a lookalike Office 365 logon page.
Once the victim offers up their credentials a “file not found” message is displayed.
Now the fun starts.
Source: Microsoft
The bad guys take the stolen credentials and attempt to log into the victims Office 365 account. Should they encounter Microsoft’s Multi-Factor Authentication, they check in with the Microsoft user agent “BAV2ROPC” which allows Exchange’s Basic Authentication (normally used in POP3/IMAP4 conditions) and results in an OAuth flow that bypasses MFA (since MFA isn’t supported for, say, an IMAP4 request). Microsoft was set to disable Basic Authentication back in October of 2020, but the pandemic put that on hold, pushing it to sometime this year.
Once into the victim’s mailbox, the bad guys use a series of forwarding rules for messages containing words like invoice, payment, or statement to a bad actor-controlled email account.
Once the scammers get a hold of emails regarding payments, it’s back to basic impersonation and social engineering tactics to convince the person or company making the payment to change banking details at the last minute.
Impersonating someone – particularly when the bad actors have access to that person’s mailbox – is tough to defend against. So, it’s critical to stop these kind of attacks well before you get to that stage. The place to stop this is at the initial phishing attack – take a look at how obvious that attachment is above; users need to be able to spot that a mile away. By enrolling them in Security Awareness Training, they will learn both the basics of good awareness, as well as the most recent scams, themes, and campaigns in use so they won’t be caught off guard when the “next” phishing attack occurs.




