 Sophos reported on one of the more scary ransomware strains I have seen lately. It's called Goldeneye and encrypts the workstation twice: both the files and the Master File Table (MFT).
Sophos reported on one of the more scary ransomware strains I have seen lately. It's called Goldeneye and encrypts the workstation twice: both the files and the Master File Table (MFT).
It's a phishing attack with two attachments. One is a PDF and the other an Excel file. The Excel file contains a loader that pulls down all the malware. The PDF is the social engineering ruse that makes the user open the Excel file. If your user is untrained enough to open both attachments and there are crucial files on the local hard disk without a backup, you potentially get to pay ransom TWICE.
The spam email presents itself as a job application form to be filled out. It has attached an uninfected PDF with the application to get the process started, and in the PDF is a polite reference that the Excel file contains more details -- no explicit demand to open up the file... just business as usual.
Opening up the Excel file, you get a suggestion how to display the aptitude test. Sophos said: "The crooks don’t openly ask you to do anything obviously risky, such “Enable macros” or “Turn off the default security configuration”, but they do encourage you to make a change to your Office settings, something that Excel will invite you to do because the file contains what are known as Visual Basic for Applications (VBA) macros.
In fact, if you permit macros to run in this Excel file, you will quickly regret it: the VBA downloads a copy of the Goldeneye ransomware and immediately launches it." The VBA programming language used in Office macros is powerful enough to allow cybercriminals to control Word or Excel programmatically, but also to perform more general actions such as downloading files from the web, saving them to disk, and running them.
Yikes.
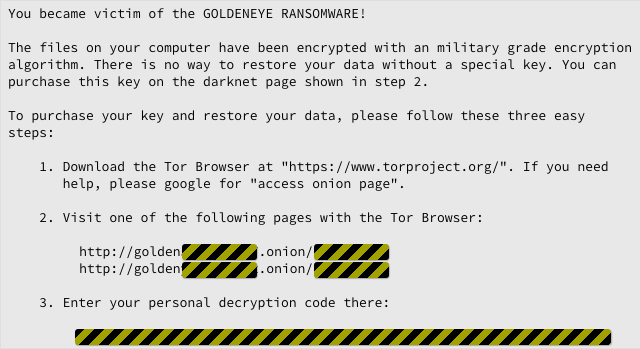
Once the Excel file is activated, all the malicious activity happens in the background, but when the encryption pass is done, there's a whole bunch of files left behind called: YOUR_FILES_ARE_ENCRYPTED.TXT which announce the infection:
Most strains of file-encrypting ransomware stop here, but Goldeneye's developer has experience in this field and does a double-whammy attack similar to their Petya / Misha strain and encrypts the Master File Table (MFT) of that machine as well.
Goldeneye works a bit different than the previous editions: it first encrypts the files, then performs the UAC bypass and the low-level MFT attack, then reboots and pretends doing a CheckDisk.
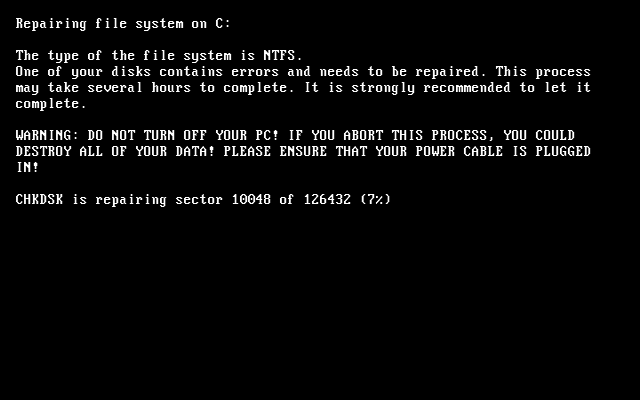
Once the “check” is finished, another reboot sounds the alarm with some dramatic ASCII art:
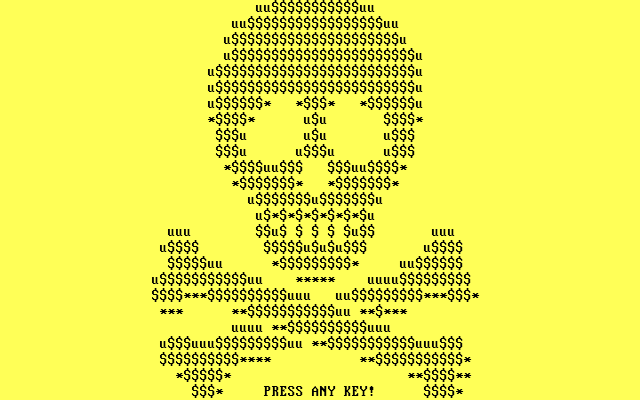
Pressing the Any Key gives you this:
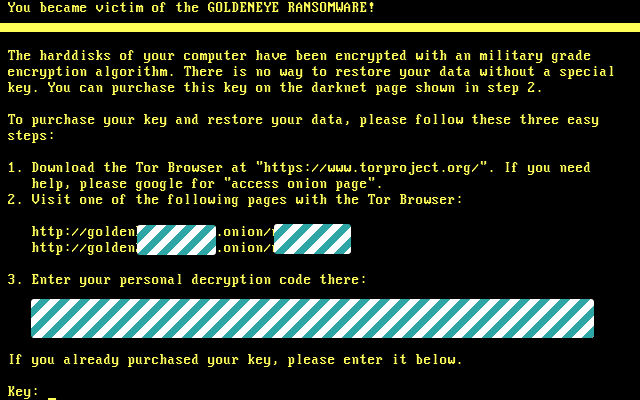
In case you’re wondering why Sophos redacted the so-called personal decryption codes in the images above, the encryption is different for your files and for your MFT: the malware uses different algorithms and different keys each time.
In short, if you pay up to unlock your scrambled MFT so you can reboot into Windows, then, assuming the crooks actually send you the key, you’ll get back into Windows only to face the YOUR_FILES_ARE_ENCRYPTED.TXT pay page as well. If you don’t have any backup, you get to pay up 1.4 Bitcoins all over again. That's 2.8 total which starts to get very expensive.
Does *Your* Antivirus block the latest Ransomware Strains?
How vulnerable is your network against ransomware attacks??
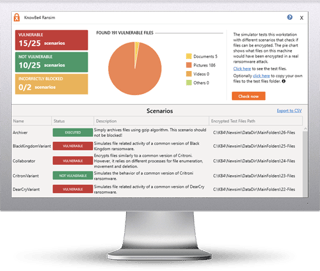
KnowBe4 has been working hard on something brand new! Bad guys are constantly coming out with new versions of ransomware strains to evade detection. Is your network effective in blocking ransomware when employees fall for social engineering attacks?
KnowBe4’s Ransomware Simulator "RanSim" gives you a quick look at the effectiveness of your existing network protection.
 Here's how RanSim works:
Here's how RanSim works:
![]() 100% harmless simulation of a real ransomware infection
100% harmless simulation of a real ransomware infection
![]() Does not use any of your own files
Does not use any of your own files
![]() Tests 10 types of infection scenarios
Tests 10 types of infection scenarios
![]() Just download the install and run it
Just download the install and run it
![]() Results in a few minutes!
Results in a few minutes!
RanSim has been downloaded thousands of times and run against dozens of AV products. The results have been an eye opening experience for many IT pros. NOTE: RanSim was created for Windows-based workstations running Windows 7 or higher.
Download RanSim Now
Don't like to click on redirected buttons? Cut & Paste this link in your browser:





