October was Cyber Security Awareness Month, the month during which many organisations and individuals contributed their ideas, shared content and helped educate each other on the importance of cybersecurity and how to remain safe.
During this month, I published several articles and videos, and delivered some presentations. As November rolled around, I almost sprained my arm patting myself on the back for a job well done before I stopped and pondered.
You see, security awareness training is not a goal or a target that you hit once and then move on with your life. Rather, it is all about changing people's behaviours so that they can make better risk decisions.
A month dedicated to cybersecurity awareness is definitely a good thing, but do you know what would be better? Taking the days from that month and spreading them all throughout the year.
For the most part, smaller, but more consistent activity yields far better results than trying to cram a lot into a small amount of time. As James Clear says in his book, “Atomic Habits,” it’s so easy to overestimate the importance of one defining moment and underestimate the value of making small improvements on a daily basis. Too often, we convince ourselves that massive success requires massive action. Meanwhile, improvement in small increments isn’t particularly noticeable, but it can be far more meaningful, especially in the long run.
Perry Carpenter also notes in his book, “Transformational Security Awareness,” that if you aren’t reinforcing, your audience is forgetting. That is to say that one of the biggest mistakes an organisation can make is only addressing security awareness as a once- or twice-per-year activity. This approach is akin to going to the gym once or twice a year and wondering why your fitness isn’t improving. It’s simply ineffective. Our opinions and behaviours aren’t generally swayed by hearing information once. We learn and change through repetition.
Nine women cannot collectively give birth to a child in one month, and you can’t expect to provide effective security awareness training to all your employees in one month either. It is why crash diets don’t work and it’s why going on a meditation retreat doesn’t lead to long term mental peace. People need consistency more than they need intensity.
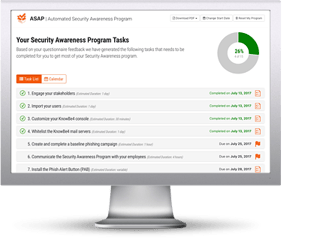
Use the intensity of Cyber Security Awareness Month as a launching point to consistency that will last throughout the year. Conduct monthly phishing tests, deliver regular training modules, have leaders discuss the importance of security in meetings and build a culture of security. That consistency is what will help you make real progress.
 Here's how it works:
Here's how it works:




