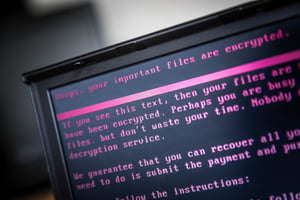
Ransomware is using a variety of methods to reduce or nullify the effectiveness of data backups, writes Maria Korolov at CSO. Restoring from a backup is one of the best strategies that organizations can use to recover from a ransomware attack, so it’s obvious why attackers would want to target this data.
Ransomware has been observed attacking shared network drives, Windows shadow copies, and any files that have backup file extensions. Some ransomware variants can even sync with the victim’s cloud service and encrypt files stored there.
Newer ransomware is also using techniques that make it harder for organizations to know which backup to restore from, according to Bob Antia, CSO of Kaseya. Ransomware that’s slow-moving and stealthy can remain undetected for weeks or months, causing confusion when it finally activates. “These two techniques mean that it's difficult to know what point in time to recover to from your backups,” says Antia. “I expect that ransomware will continue to find trickier ways to hide themselves to make recovery more difficult.”
Landon Lewis, CEO of Pondurance, says that a minimum of three backups using more than one type of backup method, with at least one copy stored off-site, is necessary to protect essential data.
Using different authentication systems and different passwords a critical part of keeping this data safe. “If your user’s account is compromised, the first thing the attacker wants to do is escalate their privileges,” Lewis says. “If the backup system uses the same authentication, they can just take over everything.”
Of course, the best way to defend your organization against ransomware is to prevent it from entering your network in the first place. In most cases, ransomware infections are caused by some fault of an employee, such as falling for a phishing email. New-school security awareness training can help your employees be cognizant of these threats.
CSO has the story: https://www.csoonline.com/article/3331981/ransomware/how-to-protect-backups-from-ransomware.html
Get Your Ransomware Hostage Rescue Manual
 This 20-page manual is packed with actionable info that you need to prevent infections, and what to do when you are hit with malware like this. You also get a Ransomware Attack Response Checklist and Prevention Checklist. You will learn more about:
This 20-page manual is packed with actionable info that you need to prevent infections, and what to do when you are hit with malware like this. You also get a Ransomware Attack Response Checklist and Prevention Checklist. You will learn more about:
- What is Ransomware?
- Am I Infected?
- I’m Infected, Now What?
- Protecting Yourself in the Future
- Resources
Don’t be taken hostage by ransomware. Download your rescue manual now!





