Cyberattackers are taking full advantage of slow patch or mitigation processes on Microsoft Exchange Server with attack rates doubling every few hours.
According to Check Point Research (CPR), threat actors are actively exploiting four zero-day vulnerabilities tackled with emergency fixes issued by Microsoft on March 2 -- and attack attempts continue to rise.
In the past 24 hours, the team has observed "exploitation attempts on organizations doubling every two to three hours."
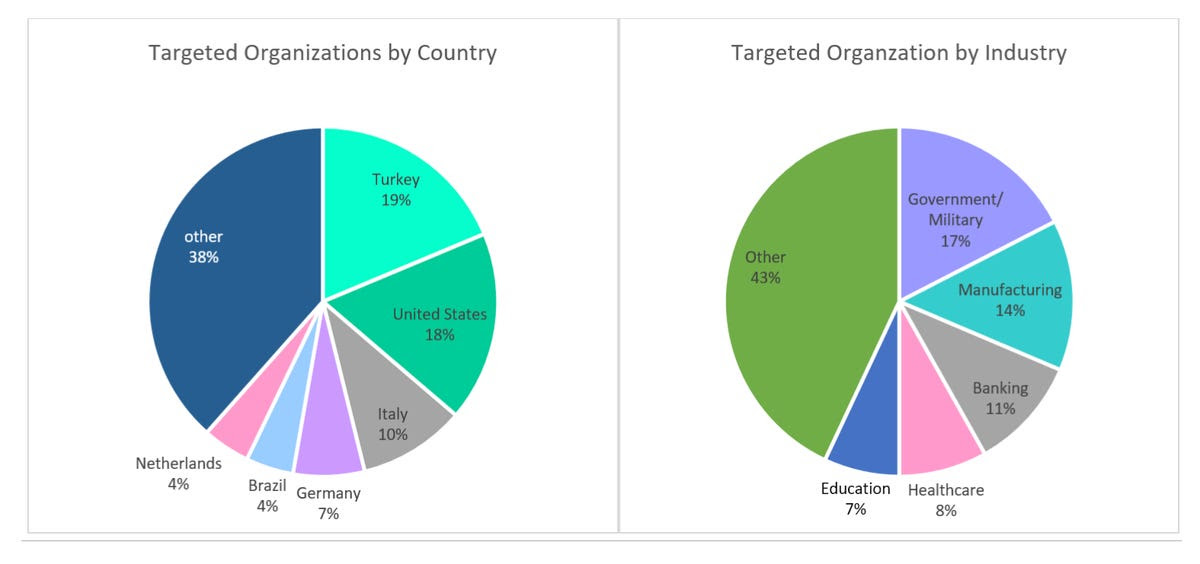
The countries feeling the brunt of attack attempts are Turkey, the United States, and Italy, accounting for 19%, 18%, and 10% of all tracked exploit attempts, respectively.
Government, military, manufacturing, and then financial services are currently the most targeted industries.
Palo Alto estimates that at least 125,000 servers remain unpatched worldwide.
The critical vulnerabilities (CVE-2021-26855, CVE-2021-26857, CVE-2021-26858, CVE-2021-27065) impact Exchange Server 2013, Exchange Server 2016, and Exchange Server 2019.
Microsoft issued emergency, out-of-band patches to tackle the security flaws -- which can be exploited for data theft and server compromise -- and has previously attributed active exploit to Chinese advanced persistent threat (APT) group Hafnium.
This week, ESET revealed at least 10 APT groups have been linked to current Microsoft Exchange Server exploit attempts.
On March 12, Microsoft said that a form of ransomware, known as DearCry, is now utilizing the server vulnerabilities in attacks. The tech giant says that after the "initial compromise of unpatched on-premises Exchange Servers" ransomware is deployed on vulnerable systems, a situation reminiscent of the 2017 WannaCry outbreak.
"Compromised servers could enable an unauthorized attacker to extract your corporate emails and execute malicious code inside your organization with high privileges," commented Lotem Finkelsteen, Manager of Threat Intelligence at Check Point. "Organizations who are at risk should not only take preventive actions on their Exchange, but also scan their networks for live threats and assess all assets." Here is the story:
https://www.zdnet.com/article/




