 Using a simple email containing a voice mail attachment, an ingenious phishing attack captures credentials while keeping track of the domains being attacked.
Using a simple email containing a voice mail attachment, an ingenious phishing attack captures credentials while keeping track of the domains being attacked.
It’s no surprise that Microsoft continues to be a brand used as part of credential-harvesting attacks, as the accounts compromised provide threat actors with access to a legitimate email address. So, this latest phishing scam identified by security researchers at Zscaler’s ThreatLabz first uses Zscaler themselves as the initial brand impersonated, and then spoofs a Microsoft 365 logon page to capture credentials.
But what makes this attack interesting is the use of multiple brand impersonation efforts, a fake voice mail message, and a unique tracking method used by the cybercriminals.
The phishing email first uses a “From” email address that aligns with the victim organization. The voice mail attachment uses a music note icon to throw off the recipient victim, but actually is an HTML attachment.
The HTML document serves as a URL redirector that points the victim to a malicious URL unique to the victim organization. According to Zscaler, the redirection URL consists of the following parts:
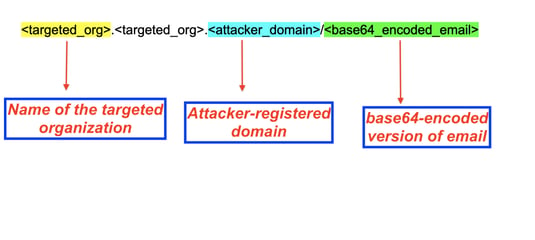
Source: Zscaler
A CAPTCHA check is used to evade URL analysis told, with the final part of the attack being the spoofed Microsoft 365 logon page.
This attack demonstrates the sophisticated efforts cybercriminals take to keep attacks from being detected and to trick users into falling victim to such scams. Security Awareness Training is an effective tool that helps users understand the methods these attacks use to fool them, empowering the user to remain vigilant when interacting with suspicious emails like the one identified by Zscaler.




