 Since the days of EternalBlue, we’ve been concerned with malware spreading within a network. The latest iterations of Matrix Ransomware use a sophisticated list of embedded tools to do its dirty work.
Since the days of EternalBlue, we’ve been concerned with malware spreading within a network. The latest iterations of Matrix Ransomware use a sophisticated list of embedded tools to do its dirty work.
The so-called “Matrix” ransomware (as named by Sohpos Labs) has been around since 2016. But, according to a new report from Sophos, the malware has undergone major recent improvements that allow it to perform a wide range of attack tasks. It uses RDP-based brute force attacks to gain an initial foothold. The malware contains several payload executables including some legitimate admin tools – each used to either infect the initial endpoint, or connect to remote machines via RDP and spread within the network. Their code even includes efforts to disable AV software on endpoints.
Once infected, the victim is required to contact the attacker, submit some encrypted files (presumably to prove they are, indeed, the victim) and then are provided with the bitcoin ransom amount equivalent to $2500.
The sophistication of the toolset included in this single instance of malware is downright scary; Matrix is a signal that cybercriminals are no longer satisfied with a single method of execution. Instead, they are arming themselves with everything they may need to act alone, potentially disconnected from any C2C server, and still be successful in not just infecting one machine – but many.
Organizations need to understand the impact malware like this can have – and take steps to prevent it from ever gaining control in their environments. Given that AV disabling tech is included (and will likely improve over time), organizations need to not so much rely on technology to detect and stop malware like this, but instead leverage Security Awareness Training to empower users to not fall victim to the phishing scams used to trick users into becoming a victim. By leveraging training like this, users become a part of the security strategy, reducing the risk of infection and ransom.
Free Ransomware Simulator Tool
How vulnerable is your network against a ransomware attack?
 Bad guys are constantly coming out with new strains to evade detection. Is your network effective in blocking all of them when employees fall for social engineering attacks?
Bad guys are constantly coming out with new strains to evade detection. Is your network effective in blocking all of them when employees fall for social engineering attacks?
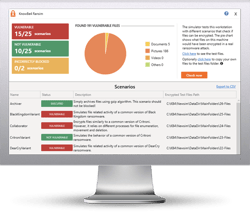
KnowBe4’s "RanSim" gives you a quick look at the effectiveness of your existing network protection. RanSim will simulate 13 ransomware infection scenarios and 1 cryptomining infection scenario and show you if a workstation is vulnerable.
PS: Don't like to click on redirected buttons? Cut & Paste this link in your browser:
https://www.knowbe4.com/ransomware-simulator





