 A man in California has been convicted for stealing $23.5 million from the US Department of Defense in a phishing attack. The Justice Department explained in a press release that the man, Sercan Oyuntur, hijacked payments meant for a jet fuel supplier.
A man in California has been convicted for stealing $23.5 million from the US Department of Defense in a phishing attack. The Justice Department explained in a press release that the man, Sercan Oyuntur, hijacked payments meant for a jet fuel supplier.
“A corporation that had a contract with the DoD to supply jet fuel to troops operating in southeast Asia employed an individual in New Jersey, who was responsible for communicating with the federal government on behalf of the corporation through a government computer system,” the Justice Department says. “Through a complex phishing scheme, Oyuntur and criminal conspirators in Germany, Turkey, and New Jersey targeted the corporation and the individual so that the conspirators could steal money that DoD intended to pay to the corporation for providing jet fuel.”
Oyuntur worked with others to set up a complex phishing operation to steal the funds.
“Oyuntur’s conspirators created fake email accounts in other people’s names and designed fake webpages that resembled the General Services Administration’s (GSA) public-facing website,” the Justice Department stated. “From June to September 2018, the conspirators caused phishing emails to be sent to various DoD vendors, including the individual from New Jersey who represented the corporation, to trick these vendors into visiting the phishing pages. These emails appeared to be legitimate communications from the United States government, but were actually sent by the conspirators, and contained electronic links that automatically took individuals to the phishing pages. There, they saw what appeared to be a GSA website and were prompted to enter their confidential login credentials, which were then used by the conspirators to make changes in the government systems and ultimately divert money to the conspirators.”
Finally, Oyuntur and his co-conspirators sent a forged government contract to trick the targeted employees into sending the money to the wrong bank account.
“On Oct. 10, 2018, based on the fraudulent activities of Oyuntur and his conspirators, DoD transferred $23.5 million that had been earned by the victim corporation into Arslan’s Deal Automotive bank account,” the Justice Department said. “Arslan went to the bank and was able to access some of this money, but the bank would not release all of the funds to Arslan. That same day, a conspirator in Turkey sent Arslan an email with an altered government contract that falsely indicated Deal Automotive had been awarded a DoD contract valued at approximately $23 million dollars. Oyuntur instructed Arslan to take this fake contract into the bank to explain why he had received the money, so that Arslan could convince the bank to release the remaining funds.”
New-school security awareness training can enable your employees to thwart targeted social engineering attacks.
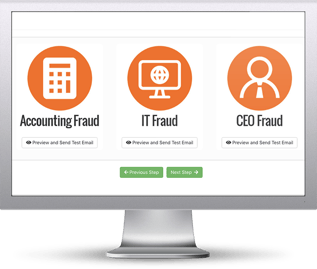 Here's how it works:
Here's how it works:




