 This blog was co-written by KnowBe4's Data-Driven Defense Evangelist Roger A. Grimes and Chief Learning Officer John Just.
This blog was co-written by KnowBe4's Data-Driven Defense Evangelist Roger A. Grimes and Chief Learning Officer John Just.
Social engineering is involved in 70% to 90% of successful compromises. It is the number one way that hackers and malware successfully attack devices and networks. No other initial root cause comes close (unpatched software and firmware are a distant second, being involved in about 33% of attacks).
A particular type of social engineering is responsible for more successful compromises than any other type of attack: spear phishing.
Last month, we reported that Barracuda Networks’ research involving real attacks against its customers showed that even though spear phishing attacks only make up only 0.1% of all email-based attacks, they are responsible for 66% of all breaches.
Let that sink in for a moment.
That means that most successful attacks are spear phishing attacks. Not that the most successful email attacks are spear phishing attacks. But those spear phishing attacks are the most successful cyber attack out there compared to everything else!
That fact should impact the way that EVERYONE does security awareness training. Luckily, we have tons of spear phishing-specific content you can use to educate your co-workers and the bottom part of this article will share some of our most popular and effective anti-spear phishing content.
What Exactly Is Spear Phishing?
Spear phishing is when a social engineering attacker uses personal or confidential information they have learned about a potential victim or organization in order to more readily trick the victim into performing a harmful action. Within that definition, spear phishing can be accomplished in thousands of different ways, ranging from basic attacks to more advanced, longer-range attacks.
Spear Phishing Examples
The average traditional spear phishing scam occurs when the attacker learns about some new confidential news or project within an organization and then uses that information to craft a new phishing email that uses the supposedly confidential information to gain trust in the new potential victim. Or the spear phishing attacker learns of some otherwise internal names and/or relationships to craft a spear phishing email with a pitch that communicates to the victim they have legitimately earned insider knowledge or relationships. For example, a spear phishing email may state something like, “I was talking to Brian in IT Security and he said I had to get with you to get my Salesforce account opened.” Or “Sheila in HR said you were the person I had to go to get that way overdue list of employee social security numbers we have to send to Kronos for processing.”
Spear phishing attacks are growing ever more sophisticated. For example, many attackers look into already compromised victim email Inboxes or Sent Item folders for useful email conversations (known as threads), which can be leveraged to trick an involved external recipient into reading a new fraudulent email purporting to be involved in the thread and motivate them into following the attacker’s requested (malicious) actions. Because the email comes from a previously trusted partner, using the partner’s real email address, using a previously used legitimate email subject, it is easier to get the trusted recipient to do a new action. For example, “Hey Bob, check out this report. It seems to exactly support what we were saying would happen on the Apple news.” It can be very difficult for new potential victims to figure out they are being pitched a new social engineering scam.
Many spear phishing scams start by abusing personal relationships outside the scope of normal business.
For example, a spear phishing attacker may learn that their victim has a particular hobby, say fishing, from the victim’s public social media postings, and then sends a message to the victim about their shared love of fishing. Since it is the victim’s loved hobby and the sender is not asking for anything suspicious, the victim is more likely to open up the unexpected message and engage with the sender. After even just a few short emails, the potential victim may begin to trust the sender more than they should, and this misplaced trust is then used by the attacker to commit a scam later on. Spear phishing email scams are harder to detect than regular non-spear phishing emails.
How To Defend Against Spear Phishing
You must use your best defense-in-depth combination of policies, technical defenses and training to prevent social engineering attacks. You have to educate everyone about the huge threat that spear phishing attacks are in the first place, and how stopping them is the most important defense they can provide to themselves and the organization.
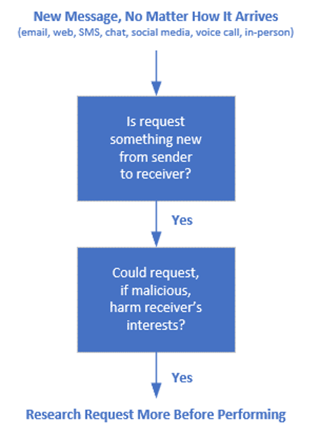
Teach co-workers to be suspicious of any new request arriving asking them to perform potentially dangerous actions, even if that request comes from a trusted source or appears to have insider information. Phishing sophistication has moved on from the early days where strange email addresses and typos could be the primary indicators of a phishing attack. Create a healthy culture of skepticism, where every co-worker confirms any unexpected request using a known legitimate method before performing the action. The key is to let your co-workers know what spear phishing is, how it differs from traditional mass audience phishing, and how to detect, report and defeat it.
For years, we have been helping you to better mitigate all social engineering attacks. Now we are going to instruct you to concentrate on spear phishing attacks with increased intensity. Whether or not your organization gets successfully phished will likely come down to how well you put down spear phishing attacks.
Within the KnowBe4 platform, we have over 100 pieces of content that cover this important topic…some are dedicated to spear phishing and some learning modules include it as part of the overall education around social engineering. One of the most popular that we see having a big effect on Phish-proneTM Percentages, is titled 2023 Social Engineering Red Flags. In this module, you get in the mindset of the attacker by hearing from a hacker where he explains how these spear phishing (among other attacks) is most often perpetrated. Another module, Spear Phishing in Action, is a very popular learning module that is highly interactive and engaging. There is also a new version of one of our most popular games that gives users a chance to practice reviewing and interacting with all kinds of phishing examples including spear phishing called Spot the Phish Game: Reloaded. Providing this sort of opportunity to practice these skills in a game-like environment is key for being prepared when an actual spear phish arrives in a user’s inbox.
We also strongly recommend training on social media attack topics and tactics. Oftentimes, attackers are successful because people overshare information on social media, leaving a virtual treasure trove for any malicious hacker.
Share with your co-workers many examples of common spear phishing attacks. KnowBe4’s educational modules contain hundreds of examples, if you are one of our customers. Then, use spear phishing-like simulated phishing tests, which include personal and confidential information, to test co-workers.
Do not let the real scammers be the only ones who are spear phishing your co-workers.




