The recent data breach of pre-IPO biotech firm Guardant Health shows how much impact a single successful phishing attack can have on an organization.
Healthcare and biotech companies hold some pretty sensitive information about their customers – name, address, driver’s license details, social security number, credit card information, and a wide range of health details. So, it stands to reason they should be pretty over-protective of that data and take every measure possible to ensure data breaches don’t occur.
In the case of Guardant Health, a single user fell victim to a phishing scam that gave cybercriminals access to the user’s email account. That was all that was needed to breach 1,100 records – and put the data breach in a spotlight originally focused solely on the company’s IPO.
Guardant Health isn’t alone – healthcare is a major target for cybercriminals, representing 24% of all data breaches. In reality, every industry vertical with valuable data remains a potential target.
The Redwood City, CA company faces potential fines and lawsuits - California’s Health Information Privacy law cite penalties as high as $250,000, and HIPAA cites civil penalties of up to $1.68 million a year and criminal penalties of up to $250,000. And, according to a recent Ponemon study, the average cost/record in a heath care-specific data breach is $408. For Guardant Health, that equates to $448,000!
Guardant included in its filing that it leverages several layers of security to protect against breaches – and yet, all it took was a single click of a phishing email to compromise a user’s email account.
Organizations need to realize their weakest link lies in its users falling prey to social engineering tactics designed to fool them into becoming an unwitting participant in a data breach, ransomware, or cryptojacking attack. The “patch” to this known vulnerability is Security Awareness Training. Users engaged in ongoing education around attacks, scams, and tactics change from being the victim to being part of your security stance. And in Guardant Health’s case, new-school Security Awareness Training probably could have helped them avoid the data breach entirely.
Cybercrime is focusing their efforts on healthcare with ransomware as the tip of the spear. You should check if your security tools protect against ransomware infections and cryptojacking.
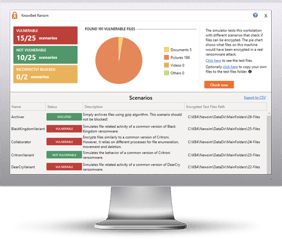
Bad guys are constantly coming out with new malware versions to evade detection. That’s why we’ve updated our Ransomware Simulated tool “RanSim” to include a new cryptomining scenario!
This new cryptomining scenario simulates a Monero cryptocurrency-mining operation on the local machine. Monero mining is the most popular cryptocurrency mined by real-world malware and takes a lot of CPU and GPU cycles to process the data necessary to generate the currencies.
Try KnowBe4’s NEW Ransomware Simulator tool and get a quick look at the effectiveness of your existing network protection against the latest threats.
RanSim will simulate 13 ransomware infection scenarios and 1 cryptomining infection scenario to show you if a workstation is vulnerable to infection.
Here's how RanSim works:
- 100% harmless simulation of real ransomware and cryptomining infection scenarios
- Does not use any of your own files
- Tests 14 different types of infection scenarios
- Just download the install and run it
- Results in a few minutes!
This is a complementary tool and will take you 5 minutes max. RanSim may give you some insights about your endpoint security you never expected!
Get the new Ransim here:
Don't like clicking on redirected buttons? Copy & paste this link into your browser:
https://info.knowbe4.com/ransomware-simulator-tool-1