 SecurityWeek reported about a Palo Alto Networks warning: "A malicious group known as the “Inception” attackers has been using a year-old Office exploit and a new backdoor in recent attacks. Active since at least 2014, the group has used custom malware and against targets spanning various industries worldwide, with a special interest in Russia.
SecurityWeek reported about a Palo Alto Networks warning: "A malicious group known as the “Inception” attackers has been using a year-old Office exploit and a new backdoor in recent attacks. Active since at least 2014, the group has used custom malware and against targets spanning various industries worldwide, with a special interest in Russia.
In October 2018, the threat actor was observed hitting various European targets in attacks employing an exploit for a vulnerability (CVE-2017-11882) that Microsoft patched in November 2017. Furthermore, the hackers were using a new PowerShell backdoor dubbed POWERSHOWER, which revealed high attention to detail in terms of cleaning up after infection.
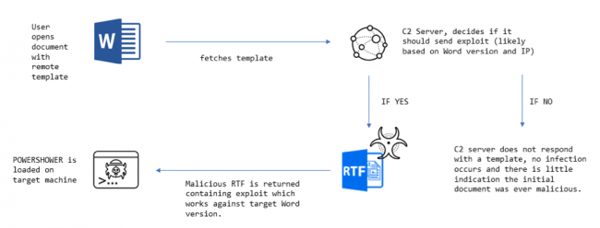
As part of the observed attacks, the actor has been using a single malicious document and a remote template to deliver their malicious payload. The use of a template was associated with the group before, but previous attacks revealed the use of two documents, including an initial spear-phishing attack for reconnaissance.
Microsoft Word allows for the loading of templates that are hosted externally, either on a file share, or on the Internet. The template is loaded as soon as the document is opened and hackers have been known to abuse the feature in malicious ways.
The Inception attackers have been using remote templates in their campaigns for the past 4 years, leveraging the various benefits the method provides, such as the fact that the initial document does not contain an explicitly malicious object.
The attack technique also provides the attacker with the option to deploy malicious content to the victim based on the initial data received from the target. This also keeps the malicious code away from researchers attempting to analyze the attack, if the hosting server is down.
The malicious document used in the recent attacks displays decoy content and attempts to fetch the remote content over HTTP. In one attack, the malicious template contained exploits for CVE-2012-1856 and CVE-2017-11882.
The payload in these attacks is POWERSHOWER, a simple PowerShell backdoor that acts as an initial reconnaissance foothold and also supports the download and execution of a secondary payload that includes a more complete set of features.
This also ensures that the more sophisticated and complex malware that the attackers might have in their portfolio remains hidden from investigators. POWERSHOWER can also clean up a significant amount of forensic evidence from the dropper process (including files and registry keys).
Full story at SecurityWeek: https://www.securityweek.com/inception-attackers-combine-old-exploit-and-new-backdoor




