Nearly half of hackers surveyed at the recent Black Hat conference in Las Vegas admitted easily compromising both Windows 8 and 10 in the past year.
In spite of the easy access through Windows, however, hackers stated their preferred method of entry to be social engineering.
The human element once again holds the key to a company’s cyber security. Training employees to think before they click while on the internet can turn what could be the weakest link into your organization's strongest last line of defense.
Fifth Domain has the story: https://www.fifthdomain.com/industry/2018/09/18/hackers-acknowledge-windows-flaws-but-prefer-social-engineering-tricks/
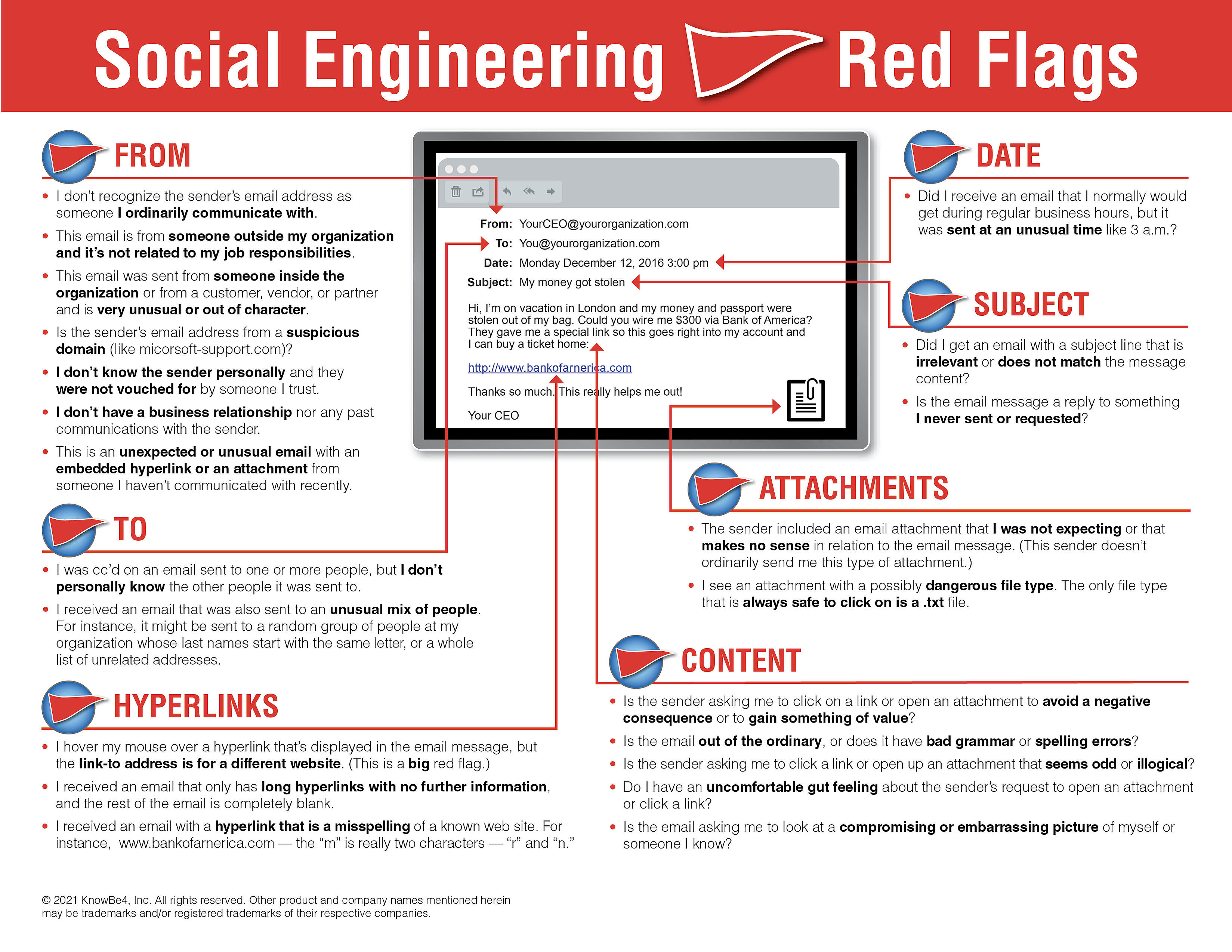
We recommend EVERYONE to review the 22 social engineering red flags to watch out for in any email. It might be a good idea to print out this PDF and pass it along to family, friends, and coworkers. Remember to always think before you click!