
Credential stuffing attacks are extremely easy to carry out and offer a massive return on investment, according to a new report by researchers at Recorded Future. These attacks utilize account-checking software to test millions of credentials leaked in data breaches against thousands of different online services. The researchers estimate that an investment of $550 can net an attacker nearly $20,000 in gross profits.
Over the past several years, credential stuffing has exploded in popularity. The efficiency of the attacks drew the attention of more sophisticated actors, who developed tools that supported custom configuration files. These plugins can be purchased, obtained for free, or developed by users themselves. Recorded Future says this development “essentially offered hackers the capability to target almost any company with an online retail presence.”
These tools are also cheap. Most sell for under $50, and several are free of charge. The profitability and success rate resulting from the widespread, automated nature of these attacks is hard to overstate.
“Although the competition quickly brought the average price of a single compromised account from over $10 down to a mere $1 to $2, the overall profitability of credential stuffing attacks increased significantly through sheer volume,” the researchers write.
Given the number of online services the average employee re-uses, combined with the massive amount of breached credentials available online, the researchers say that it’s “safe to assume that almost every large organization with an online retail presence has had their users exposed to credential stuffing attacks in the past few years.”
To defend against this threat, Recorded Future recommends that users implement multi-factor authentication and use a password manager to generate unique passwords for each of their accounts. New-school security awareness training can equip your employees with the knowledge necessary to defend themselves against these attacks in their professional and personal lives. Recorded Future has the story: https://www.recordedfuture.com/credential-stuffing-attacks/
 How weak are your user’s passwords? Are they... P@ssw0rd?
How weak are your user’s passwords? Are they... P@ssw0rd?
Verizon's recent Data Breach Report showed that 81% of hacking-related breaches used either stolen and/or weak passwords. Employees are the weakest link in your network security, using weak passwords and falling for phishing and social engineering attacks.
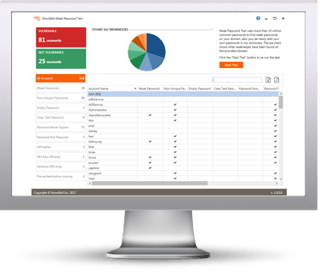
KnowBe4’s complimentary Weak Password Test (WPT) checks your Active Directory for several different types of weak password related threats.
WPT gives you a quick look at the effectiveness of your password policies and any fails so that you can take action. WPT tests against 10 types of weak password related threats for example; Weak, Duplicate, Empty, Never Expires, plus 6 more.
Here's how Weak Password Test works:
- Reports on the accounts that are affected
- Tests against 10 types of weak password related threats
- Does not show/report on the actual passwords of accounts
- Just download the install and run it
- Results in a few minutes!
This will take you 5 minutes and may give you some insights you never expected!
Download Now:





