 A mere blip on the ransomware radar a quarter ago, the massive onslaught of attacks using Hive Ransomware demonstrates how dangerous the “as-a-Service” model really is.
A mere blip on the ransomware radar a quarter ago, the massive onslaught of attacks using Hive Ransomware demonstrates how dangerous the “as-a-Service” model really is.
If you looked at the industry data a quarter ago, Hive ransomware only represented 2.5% of all attacks. But this up-and-coming new ransomware variant is a blueprint of just how easy it can be for affiliates to setup shop, download the ransomware, and collect on their bounty.
According to a recent look into the Hive by security researchers at GroupIB, the Hive is making ransomware easy. Affiliates can generate a unique version of the ransomware in less than 15 minutes, victim companies can be registered into the Hive’s backend (much like a software partner registering a customer in a partner portal to ensure the deal is attributed to the partner), and transparency is key; with the Hive making sure all communications with victims also visible to affiliates.
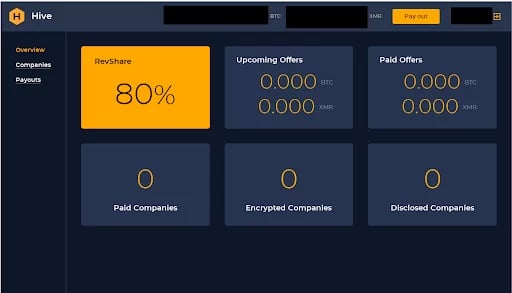
Source: The Hive Affiliate Program home page
This is a well-oiled machine. And that’s scary.
Hive is responsible for the single largest ransom demand to date - $240 Million – made in November of last year to electronics retail giant MediaMarkt. This should tell you that the Hive is only going to grow its’ operations and be a formidable tool in the belt of affiliate cybercriminals.
The good news is Hive attacks traditionally use spear-phishing attacks as their initial attack vector. This means that effective Security Awareness Training can do a lot to thwart phishing attacks that use social engineering tactics to trick victims into engaging with malicious loaders that will, inevitably release the Hive.
Be on the watch for this one… it’s going to sting.
 Here's how it works:
Here's how it works:




