 Ransomware is now one of the greatest threats on the internet.
Ransomware is now one of the greatest threats on the internet.
In the past, IT Security firms used to monitor spear-phishing attacks by espionage outfits, but these techniques are now being adopted in the criminal field and greatly contribute to their effectiveness: mass spear-phishing, meet ransomware!
In a spear-phishing attack, threat actors use a deep knowledge of the potential victims to target them, and that approach allows them to tailor the attack.
According to security experts at Proofpoint, a threat actor called the TA530 group has been targeting executives and other high-level employees in an attempt to compromise their machine with various malware, including the CryptoWall ransomware.
Other malware spread in the campaign includes the Ursnif ISFB banking trojan and the Ursnif/RecoLoad point of sale reconnaissance trojan targeting businesses in the retail and hospitality industries. Targeted executives typically have titles of chief financial officer, head of finance, senior vice president, and director.
According to new research:
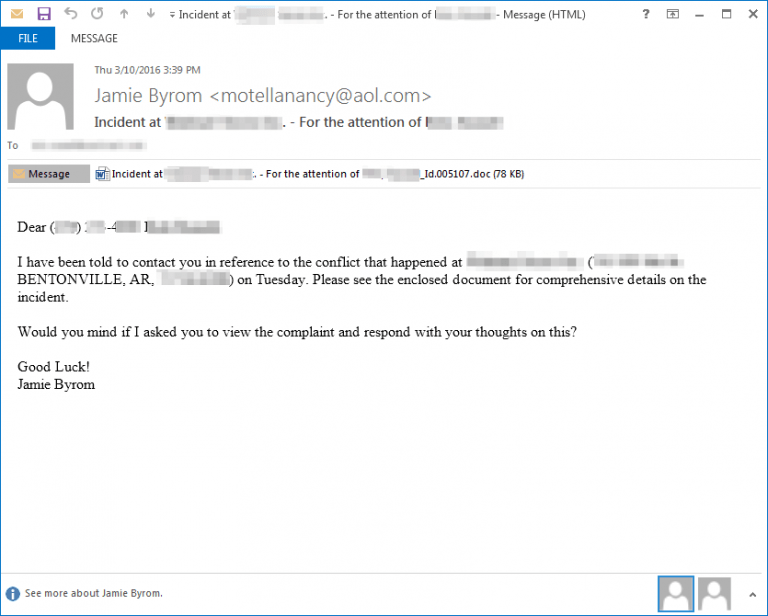
"TA530 customizes the e-mail to each target by specifying the target’s name, job title, phone number, and company name in the email body, subject, and attachment names. On several occasions, we verified that these details are correct for the intended victim. While we do not know for sure the source of these details, they frequently appear on public websites, such as LinkedIn or the company’s own website. The customization doesn't end with the lure; the malware used in the campaigns is also targeted by region and vertical.
"While these campaigns aren't approaching the size of, for example, Dridex and Locky blasts that go after very large numbers of random recipients, TA530 targets hundreds, thousands, or even tens of thousands of recipients in US, UK, and Australian organizations. These attacks are quite large relative to other selective or spear phishing campaigns.
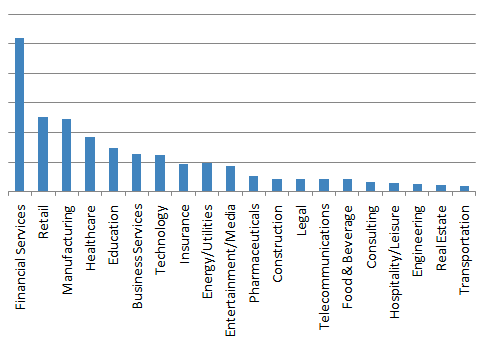
"We observed TA530 at times targeting only a specific and narrow vertical, such as Retail and Hospitality. At other times, the campaigns appear more widespread. Overall, the volume of messages targeting each vertical is shown below:"
"Based on what we have seen in these examples from TA530, we expect this actor to continue to use personalization and to diversify payloads and delivery methods. The personalization of email messages is not new, but this actor seems to have incorporated and automated a high level of personalization, previously not seen at this scale, in their spam campaigns", the proofpoint blog concludes.
Have a look at this example, with personalized information grayed out. This is very sophisticated!
We can most definitely expect threat actors to further develop efforts in mass spear phishing campaigns as they are much more profitable than 'spray and pray' phishing campaigns. This is only one of many threats that make it so important for all users to have the proper training that can prevent a costly attack.
As you can see, your execs have a target on their back and need to be stepped through effective security awareness training as soon as possible. Find out how affordable this is, and be pleasantly surprised.





