 After a deadline was missed for receiving a ransom payment, the group behind Maze Ransomware has published almost 700 MB worth of data and files stolen from a security staffing firm. Our friend Larry Abrams at Bleepingcomputer was told this is only 10% of the total files stolen and the rest will be released if a payment is not made. This is an unfortunate story and one that Bleepingcomputer does not enjoy telling, but with Maze's actions it is important to be told because this is something everyone needs to be aware of.
After a deadline was missed for receiving a ransom payment, the group behind Maze Ransomware has published almost 700 MB worth of data and files stolen from a security staffing firm. Our friend Larry Abrams at Bleepingcomputer was told this is only 10% of the total files stolen and the rest will be released if a payment is not made. This is an unfortunate story and one that Bleepingcomputer does not enjoy telling, but with Maze's actions it is important to be told because this is something everyone needs to be aware of.
Ransomware Infection = Data Breach
With this escalated attack, ransomware victims now need to not only be concerned about recovering their encrypted files, but what would happen if their stolen unencrypted files were leaked to the public, and the fact that ransomware infections by now probably should be disclosed as a data breach with all related consequences.
MAZE Ransomware Crew Contacts Bleepingcomputer
Maze is a ransomware infection that been operating for some time, but has become increasingly more active since May 2019. The group of actors behind Maze are also more known and were labeled as TA2101 after conducting numerous malspam campaigns that impersonate government agencies.
Here is what the criminals wrote:
"I am writing to you because we have breached [REDACTED], downloaded data and executed Maze ransomware in their network.
They were asked to pay ransom in order to get decryptor and be safe from data leakage, we have also told them that we would write to you about this situation if they dont pay us, because it is a shame for the security firm to get breached and ransomwared.
We gave them time to think until this day, but it seems they abandoned payment process.
I uploaded some files from their network as the data breach proofs. If they dont begin sending requested money until next Friday we will begin releasing on public everything that we have downloaded from their network before running Maze."
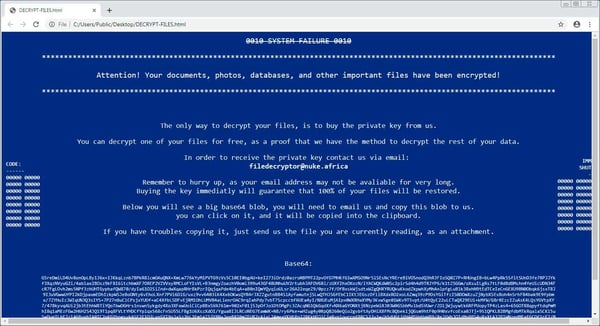
There was evidence attached, a small sample of file that were allegedly stolen from the victim. In further conversations, the Maze actors told Bleepingcomputer that they encrypted 'a lot' of computers and are demanding 300 bitcoins, or approximately $2.3 million USD, to decrypt the entire network.
Abrams commented: "Furthermore, with ransomware actors actively searching through files on a victim's machines in order to further extort their victims, in many cases these attacks should now be considered data breaches. This leads to an escalated cost of dealing with breach notifications, hiring data breach lawyers, and the potential lawsuits that may follow. It is too soon to tell if this tactic will prove fruitful, but this is definitely something we will need to keep an eye on going forward."
Unfortunately we agree, this is a new escalated reality that is setting in.
How Does Maze Get Inside?
Apparently these are sophisticated players. They are known to use exploit kits, so make sure you have all the latest Windows security updates installed and that your applications are updated to the latest versions. Apparently they are also using hacked RDP services so make sure those are also locked down tight. I would not be surprised if they use phishing as well.
Five Things You Can Do About This Right Away:
- When is the last time you tested the restore function of your backups? You want to do that ASAP, and make sure you have weapons-grade backups at all times.
- Scan your network to identify any open RDP ports and ideally disable RDP completely on all Windows machines if possible. By default, the server listens on TCP port 3389 and UDP port 3389.
- Best practice to protect a network from a brute force RDP attack is to apply strong RDP security settings, including limiting or disabling access to shared folders and clipboards from remote locations.
- An RDP brute force approach does open the attacker’s information to the targeted network, so automate the process of parsing the Windows Event Viewer logs, find any compromised user accounts, identify the IP address of the attacker and block that.
- Do a no-charge Phishing Security Test and find out what percentage of your users is Phish-prone. Use that percentage as a catalyst to start a new-school security awareness training program, which—by survey—your users are actually going to appreciate because it helps them stay safe on the internet at the house. PS, the password is "homecourse". It's free.




