
The World Health Organization (WHO) is putting out an alert about ongoing Coronavirus-themed phishing attacks that impersonate the WHO and try to steal confidential information and deliver malware. This is exactly what we predicted.
"Criminals are disguising themselves as WHO to steal money or sensitive information," the United Nations agency says in the Coronavirus scam alert.
"WHO is aware of suspicious email messages attempting to take advantage of the 2019 novel coronavirus emergency."
The phishing messages are camouflaged to appear as being sent by WHO officials and ask the targets to share sensitive info like usernames and passwords, redirect them to a phishing landing page via malicious links embedded in the emails, or ask them to open malicious attachments containing malware payloads. "If you are contacted by a person or organization that appears to be from WHO, verify their authenticity before responding," says the WHO.
WHO phishing campaign
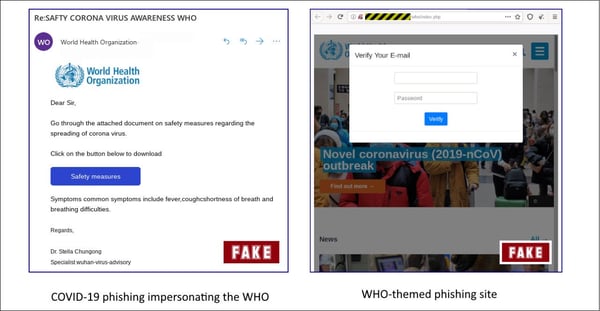
An example of such a phishing campaign using COVID-19 as bait and asking potential victims to "go through the attached document on safety measures regarding the spreading of coronavirus" was spotted by the Sophos Security Team earlier this month.
They were also asked to download the attachment to their computer by clicking on a "Safety Measures" button that would instead redirect them to a compromised site the attackers use as a phishing landing page.
This phishing page loads the WHO website in a frame in the background and displays a pop-up in the foreground asking the targets to verify their e-mail.
Once they write in their usernames and passwords and click the "Verify" button, their credentials will be exfiltrated to a server controlled by the attackers over an unencrypted HTTP connection and redirect them to WHO's official website — not that the phishers would care about their victims' data security. Here is how it looks:
If you have not done this yet, I would send your employees, friends and family something like the following. Feel free to copy/paste/edit.
"The worldwide spread of the new Coronavirus is being used by bad guys to scare people into clicking on links, open malicious attachments, or give out confidential information. Be careful with anything related to the Coronavirus: emails, attachments, any social media, texts on your phone, anything. Look out for topics like:
- Check updated Coronavirus map in your city
- Coronavirus Infection warning from local school district
- CDC or World Health Organization emails or social media Coronavirus messaging
- Keeping your children safe from Coronavirus
- You might even get a scam phone call to raise funds for "victims".
There will be a number of scams related to this, so please remember to Think Before You Click!
For KnowBe4 Customers, you can find a Coronavirus-themed simulated phishing template in the Current Events category. I suggest you send to your employees and friends / family more or less immediately.
Let's stay safe out there.
Warm regards,
Stu Sjouwerman
Founder and CEO, KnowBe4, Inc.





